Adaface Sample Cyber Security Questions
Here are some sample Cyber Security questions from our premium questions library (10273 non-googleable questions).
Skills
Aptitude & Soft Skills
Logical Reasoning
Abstract Reasoning
English
Reading Comprehension
Spatial Reasoning
Verbal Reasoning
Diagrammatic Reasoning
Critical Thinking
Data Interpretation
Situational Judgement
Attention to Detail
Numerical Reasoning
Aptitude
Quantitative Reasoning
Inductive Reasoning
Deductive Reasoning
Error Checking
English Speaking
Pronunciation
Product & Design
Visualization & BI Tools
Programming Languages
Frontend Development
Backend Development
Data Science & AI
Data Engineering & Databases
Cloud & DevOps
Testing & QA
Accounting & Finance
Microsoft & Power Platform
CRM & ERP Platforms
Cybersecurity & Networking
Marketing & Growth
Oracle Technologies
Other Tools & Technologies
| 🧐 Question | |||||
|---|---|---|---|---|---|
|
Medium
Cookie Security Analysis
|
Solve
|
||||
|
|
|||||
|
Medium
Security Incident
|
Solve
|
||||
|
|
|||||
|
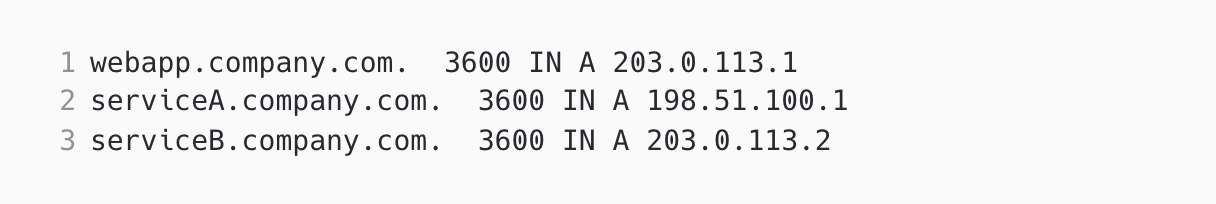
Medium
Network Traffic Anomaly
|
Solve
|
||||
|
|
|||||
|
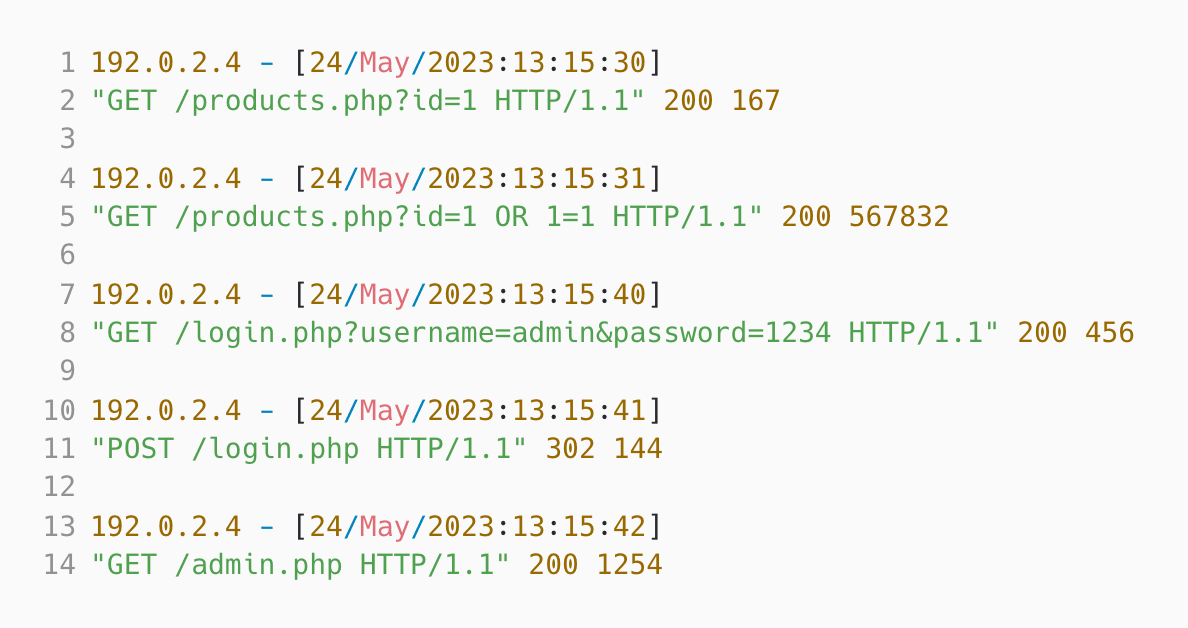
Medium
SQL Log Analysis
|
Solve
|
||||
|
|
|||||
|
Medium
Misappropriation Post-Migration
|
Solve
|
||||
|
|
|||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
|
Medium
Cookie Security Analysis
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
Security Incident
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
Network Traffic Anomaly
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
SQL Log Analysis
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
Misappropriation Post-Migration
|
3 mins Cyber Security
|
Solve
|
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
|
Cookie Security Analysis
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
Security Incident
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
Network Traffic Anomaly
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
SQL Log Analysis
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
Misappropriation Post-Migration
|
Cyber Security
|
Medium | 3 mins |
Solve
|
We evaluated several of their competitors and found Adaface to be the most compelling. Great library of questions that are designed to test for fit rather than memorization of algorithms.
Swayam Narain, CTO, Affable


Join 1200+ companies in 80+ countries.
Try the most candidate friendly skills assessment tool today.

Ready to streamline your recruitment efforts with Adaface?
Ready to streamline your recruitment efforts with Adaface?