Test Duration
~ 40 分
Difficulty Level
Moderate
Questions
- 5 Ethical Hacking MCQs
- 5 サイバーセキュリティ MCQs
- 5 コンピューターネットワーク MCQs
Availability
Available on request
About the test:
倫理的ハッキングテストは、サイバーセキュリティ、ネットワークセキュリティ、Webアプリケーションセキュリティ、ワイヤレスセキュリティなどのトピックに焦点を当てた倫理的ハッキングに関する候補者の知識とスキルを評価します。このテストでは、脆弱性を特定し、セキュリティの欠陥を活用し、不正アクセスを防ぎ、機密情報を保護するための効果的なソリューションを提供する候補者の能力を評価します。
Covered skills:
Test Duration
~ 40 分
Difficulty Level
Moderate
Questions
Availability
Available on request
The Ethical Hacking Test helps recruiters and hiring managers identify qualified candidates from a pool of resumes, and helps in taking objective hiring decisions. It reduces the administrative overhead of interviewing too many candidates and saves time by filtering out unqualified candidates at the first step of the hiring process.
The test screens for the following skills that hiring managers look for in candidates:
Traditional assessment tools use trick questions and puzzles for the screening, which creates a lot of frustration among candidates about having to go through irrelevant screening assessments.
The main reason we started Adaface is that traditional pre-employment assessment platforms are not a fair way for companies to evaluate candidates. At Adaface, our mission is to help companies find great candidates by assessing on-the-job skills required for a role.
Why we started AdafaceWe have a very high focus on the quality of questions that test for on-the-job skills. Every question is non-googleable and we have a very high bar for the level of subject matter experts we onboard to create these questions. We have crawlers to check if any of the questions are leaked online. If/ when a question gets leaked, we get an alert. We change the question for you & let you know.
How we design questionsこれらは、10,000以上の質問のライブラリからのわずかなサンプルです。これに関する実際の質問 倫理的ハッキングテスト グーグルできません.
| 🧐 Question | |||||
|---|---|---|---|---|---|
Medium Cookie Security Analysis | Try practice test | ||||
Medium Security Incident | Try practice test | ||||
Medium Network Traffic Anomaly | Try practice test | ||||
Medium SQL Log Analysis | Try practice test | ||||
Medium Misappropriation Post-Migration | Try practice test | ||||
Medium Mac address and IP on router hop | Try practice test | ||||
Easy MX Record, DMARC and Email Authentication | Try practice test | ||||
Medium Remote network resources | Try practice test | ||||
Medium SSL Certificate Expiry | Try practice test | ||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
Medium Cookie Security Analysis | 2 mins Cyber Security | Try practice test | |
Medium Security Incident | 2 mins Cyber Security | Try practice test | |
Medium Network Traffic Anomaly | 2 mins Cyber Security | Try practice test | |
Medium SQL Log Analysis | 2 mins Cyber Security | Try practice test | |
Medium Misappropriation Post-Migration | 3 mins Cyber Security | Try practice test | |
Medium Mac address and IP on router hop | 2 mins Computer Networks | Try practice test | |
Easy MX Record, DMARC and Email Authentication | 2 mins Computer Networks | Try practice test | |
Medium Remote network resources | 3 mins Computer Networks | Try practice test | |
Medium SSL Certificate Expiry | 2 mins Computer Networks | Try practice test |
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
Cookie Security Analysis | Cyber Security | Medium | 2 mins | Try practice test | |
Security Incident | Cyber Security | Medium | 2 mins | Try practice test | |
Network Traffic Anomaly | Cyber Security | Medium | 2 mins | Try practice test | |
SQL Log Analysis | Cyber Security | Medium | 2 mins | Try practice test | |
Misappropriation Post-Migration | Cyber Security | Medium | 3 mins | Try practice test | |
Mac address and IP on router hop | Computer Networks | Medium | 2 mins | Try practice test | |
MX Record, DMARC and Email Authentication | Computer Networks | Easy | 2 mins | Try practice test | |
Remote network resources | Computer Networks | Medium | 3 mins | Try practice test | |
SSL Certificate Expiry | Computer Networks | Medium | 2 mins | Try practice test |
Adaface を使用することで、最初の選考プロセスを 75% 以上最適化することができ、採用担当マネージャーと人材獲得チームの両方にとって貴重な時間を同様に解放することができました。
Brandon Lee, 人々の責任者, Love, Bonito
The most important thing while implementing the pre-employment 倫理的ハッキングテスト in your hiring process is that it is an elimination tool, not a selection tool. In other words: you want to use the test to eliminate the candidates who do poorly on the test, not to select the candidates who come out at the top. While they are super valuable, pre-employment tests do not paint the entire picture of a candidate’s abilities, knowledge, and motivations. Multiple easy questions are more predictive of a candidate's ability than fewer hard questions. Harder questions are often "trick" based questions, which do not provide any meaningful signal about the candidate's skillset.
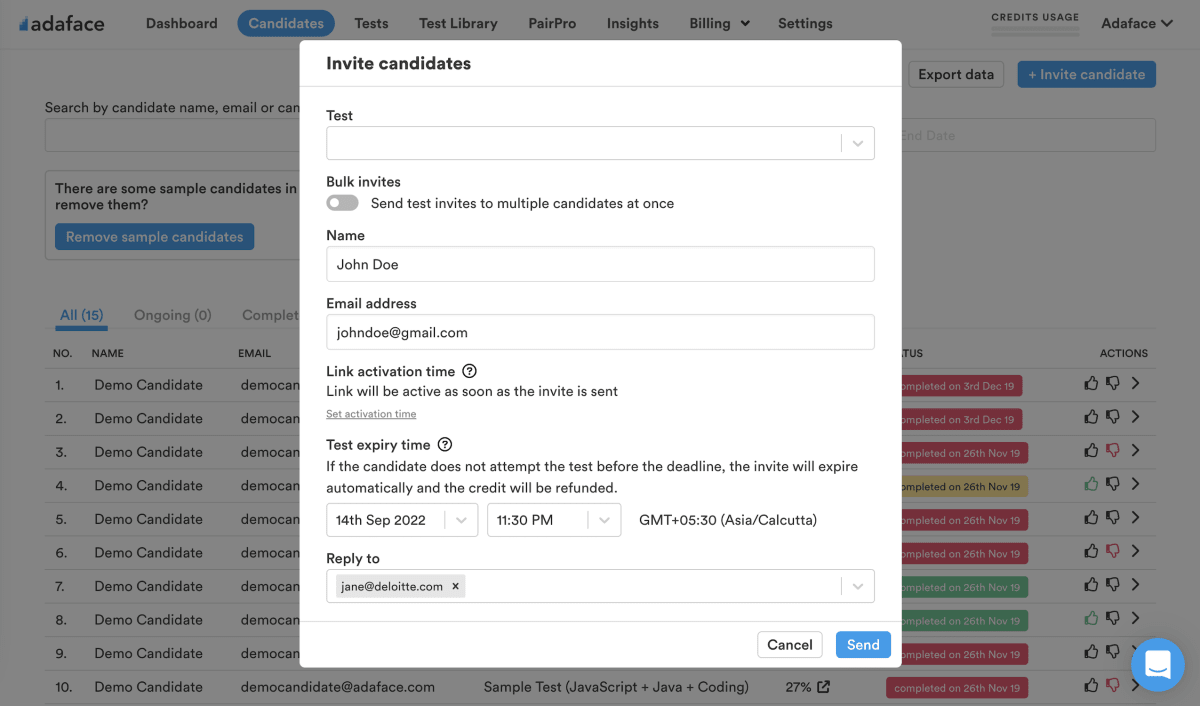
Science behind Adaface testsEmail invites: You can send candidates an email invite to the 倫理的ハッキングテスト from your dashboard by entering their email address.
Public link: You can create a public link for each test that you can share with candidates.
API or integrations: You can invite candidates directly from your ATS by using our pre-built integrations with popular ATS systems or building a custom integration with your in-house ATS.
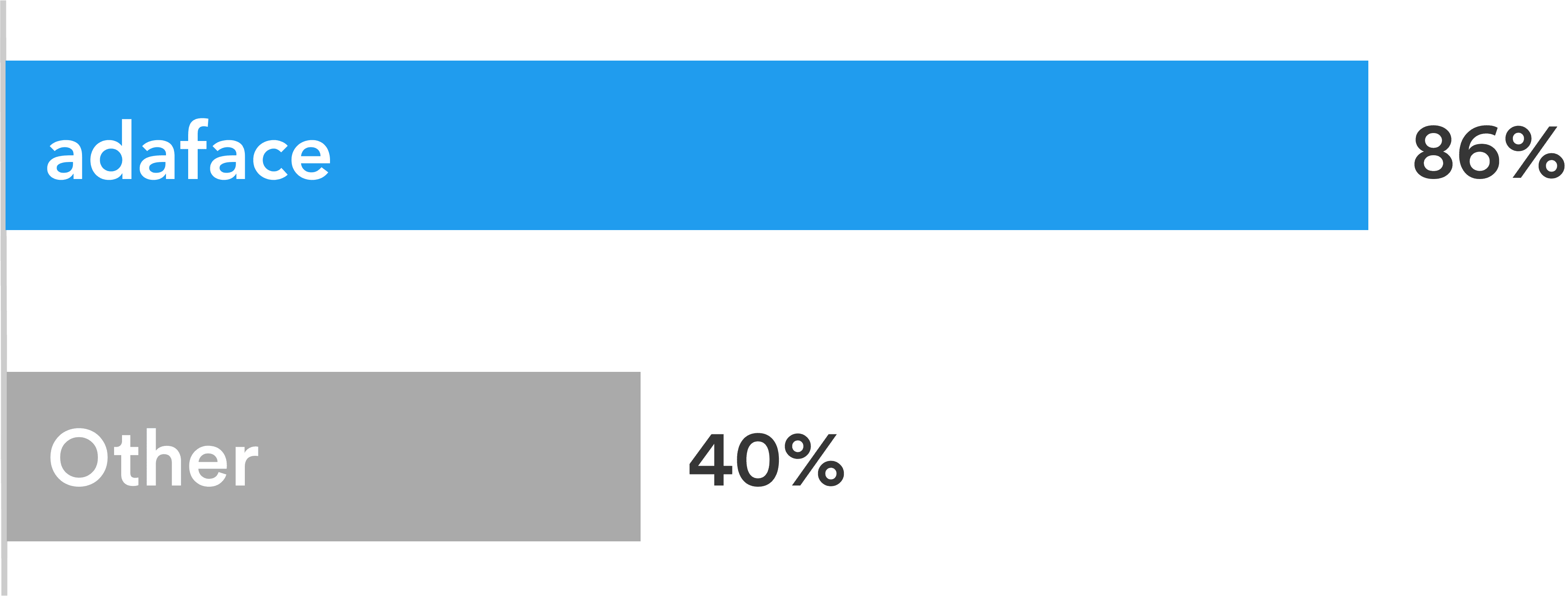
Adaface tests are conversational, low-stress, and take just 25-40 mins to complete.
This is why Adaface has the highest test-completion rate (86%), which is more than 2x better than traditional assessments.
ChatGPT protection
Screen proctoring
Plagiarism detection
Non-googleable questions
User authentication
IP proctoring
Web proctoring
Webcam proctoring
Full screen proctoring
Copy paste protection
採用担当者は、パネル面接中に尋ねる専門的な質問を通じて、どの候補者がより良いスコアを持っているかを判断し、スコアがそれほど高くない候補者と区別できると感じました。彼らです 非常に満足 Adaface のスクリーニングで最終候補者リストに選ばれた候補者の質を重視します。
そのとおり。カスタム評価は、職務内容に基づいて設定され、指定したすべての必須スキルに関する質問が含まれます。
次のアンチチート機能があります。
[プロクチャリング機能](https://www.adaface.com/proctoring)の詳細をご覧ください。
留意すべき主なことは、評価が選択ツールではなく排除ツールであることです。スキル評価が最適化され、技術的にその役割の資格がない候補者を排除するのに役立ちます。これは、役割の最良の候補者を見つけるのに役立つために最適化されていません。したがって、評価を使用する理想的な方法は、しきい値スコア(通常は55%、ベンチマークを支援します)を決定し、インタビューの次のラウンドのしきい値を超えてスコアを上回るすべての候補者を招待することです。
各ADAFACE評価は、職務記述書/理想的な候補者のペルソナにカスタマイズされます(当社の主題の専門家は、10000以上の質問のライブラリからあなたの評価に適切な質問を選択します)。この評価は、あらゆる経験レベルでカスタマイズできます。
はい、候補者を比較するのがはるかに簡単になります。 MCQの質問と質問の順序のオプションはランダム化されます。 [https://www.adaface.com/proctoring)機能を備えている[アンチチート/監督](https://www.adaface.com/proctoring)があります。エンタープライズプランでは、同様の難易度の問題を伴う同じ評価の複数のバージョンを作成するオプションもあります。
いいえ。残念ながら、現時点では練習テストをサポートしていません。ただし、[サンプルの質問](https://www.adaface.com/questions)を使用するには、練習できます。
ADAFACEの[カスタム評価をリクエストする方法](https://help.adaface.com/en/articles/6324286-requesting-a-custom-test)に関するクイックガイドを示します。