Test Duration
~ 40 Mins
Difficulty Level
Moderate
Questions
- 5 Ethical Hacking MCQs
- 5 Cíber segurança MCQs
- 5 Redes de computadores MCQs
Availability
Available on request
About the test:
O teste ético de hackers avalia o conhecimento e as habilidades de um candidato em hackers éticos, com foco em tópicos como segurança cibernética, segurança de rede, segurança de aplicativos da Web e segurança sem fio. O teste avalia a capacidade do candidato de identificar vulnerabilidades, explorar falhas de segurança e fornecer soluções eficazes para impedir o acesso não autorizado e proteger informações sensíveis.
Covered skills:
Test Duration
~ 40 Mins
Difficulty Level
Moderate
Questions
Availability
Available on request
The Ethical Hacking Test helps recruiters and hiring managers identify qualified candidates from a pool of resumes, and helps in taking objective hiring decisions. It reduces the administrative overhead of interviewing too many candidates and saves time by filtering out unqualified candidates at the first step of the hiring process.
The test screens for the following skills that hiring managers look for in candidates:
Traditional assessment tools use trick questions and puzzles for the screening, which creates a lot of frustration among candidates about having to go through irrelevant screening assessments.
The main reason we started Adaface is that traditional pre-employment assessment platforms are not a fair way for companies to evaluate candidates. At Adaface, our mission is to help companies find great candidates by assessing on-the-job skills required for a role.
Why we started AdafaceWe have a very high focus on the quality of questions that test for on-the-job skills. Every question is non-googleable and we have a very high bar for the level of subject matter experts we onboard to create these questions. We have crawlers to check if any of the questions are leaked online. If/ when a question gets leaked, we get an alert. We change the question for you & let you know.
How we design questionsEstes são apenas uma pequena amostra da nossa biblioteca de mais de 10.000 perguntas. As perguntas reais sobre isso Teste de hackers éticos será não-googleable.
| 🧐 Question | |||||
|---|---|---|---|---|---|
Medium Cookie Security Analysis | Solve | ||||
Medium Security Incident | Solve | ||||
Medium Network Traffic Anomaly | Solve | ||||
Medium SQL Log Analysis | Solve | ||||
Medium Misappropriation Post-Migration | Solve | ||||
Medium Mac address and IP on router hop | Solve | ||||
Easy MX Record, DMARC and Email Authentication | Solve | ||||
Medium Remote network resources | Solve | ||||
Medium SSL Certificate Expiry | Solve | ||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
Medium Cookie Security Analysis | 2 mins Cyber Security | Solve | |
Medium Security Incident | 2 mins Cyber Security | Solve | |
Medium Network Traffic Anomaly | 2 mins Cyber Security | Solve | |
Medium SQL Log Analysis | 2 mins Cyber Security | Solve | |
Medium Misappropriation Post-Migration | 3 mins Cyber Security | Solve | |
Medium Mac address and IP on router hop | 2 mins Computer Networks | Solve | |
Easy MX Record, DMARC and Email Authentication | 2 mins Computer Networks | Solve | |
Medium Remote network resources | 3 mins Computer Networks | Solve | |
Medium SSL Certificate Expiry | 2 mins Computer Networks | Solve |
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
Cookie Security Analysis | Cyber Security | Medium | 2 mins | Solve | |
Security Incident | Cyber Security | Medium | 2 mins | Solve | |
Network Traffic Anomaly | Cyber Security | Medium | 2 mins | Solve | |
SQL Log Analysis | Cyber Security | Medium | 2 mins | Solve | |
Misappropriation Post-Migration | Cyber Security | Medium | 3 mins | Solve | |
Mac address and IP on router hop | Computer Networks | Medium | 2 mins | Solve | |
MX Record, DMARC and Email Authentication | Computer Networks | Easy | 2 mins | Solve | |
Remote network resources | Computer Networks | Medium | 3 mins | Solve | |
SSL Certificate Expiry | Computer Networks | Medium | 2 mins | Solve |
Com o Adaface, conseguimos otimizar nosso processo de seleção inicial em mais de 75%, liberando um tempo precioso tanto para os gerentes de contratação quanto para nossa equipe de aquisição de talentos!
Brandon Lee, Chefe de Pessoas, Love, Bonito
The most important thing while implementing the pre-employment Teste de hackers éticos in your hiring process is that it is an elimination tool, not a selection tool. In other words: you want to use the test to eliminate the candidates who do poorly on the test, not to select the candidates who come out at the top. While they are super valuable, pre-employment tests do not paint the entire picture of a candidate’s abilities, knowledge, and motivations. Multiple easy questions are more predictive of a candidate's ability than fewer hard questions. Harder questions are often "trick" based questions, which do not provide any meaningful signal about the candidate's skillset.
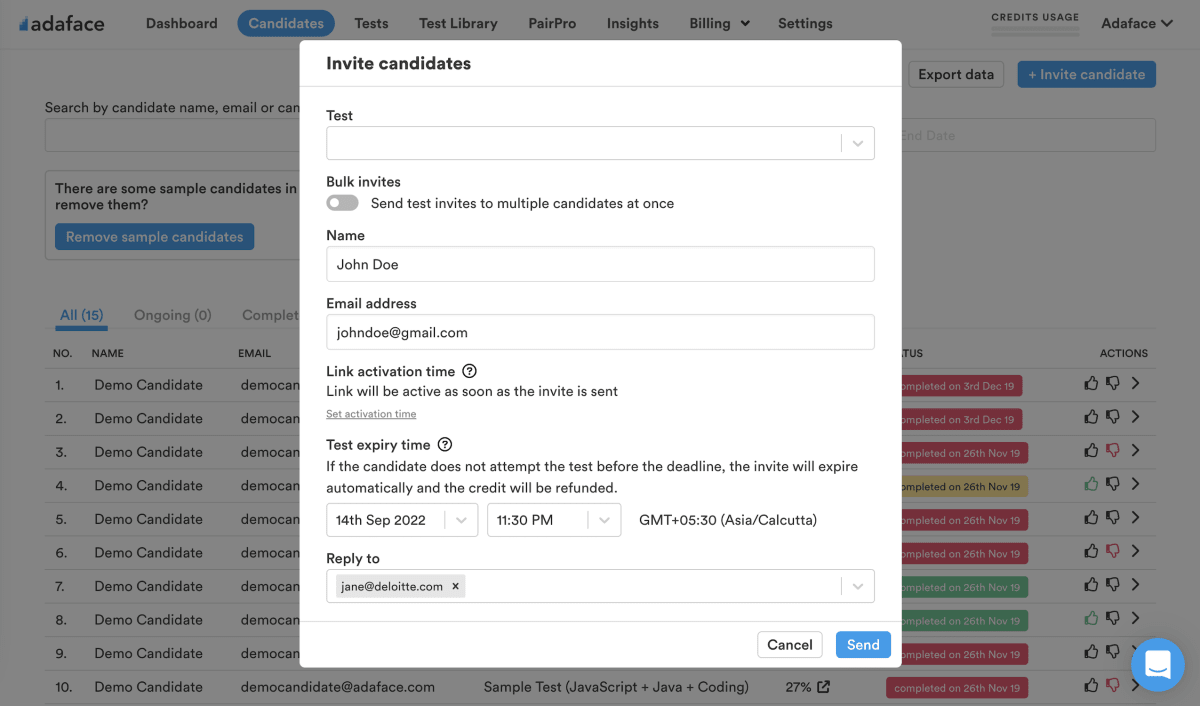
Science behind Adaface testsEmail invites: You can send candidates an email invite to the Teste de hackers éticos from your dashboard by entering their email address.
Public link: You can create a public link for each test that you can share with candidates.
API or integrations: You can invite candidates directly from your ATS by using our pre-built integrations with popular ATS systems or building a custom integration with your in-house ATS.
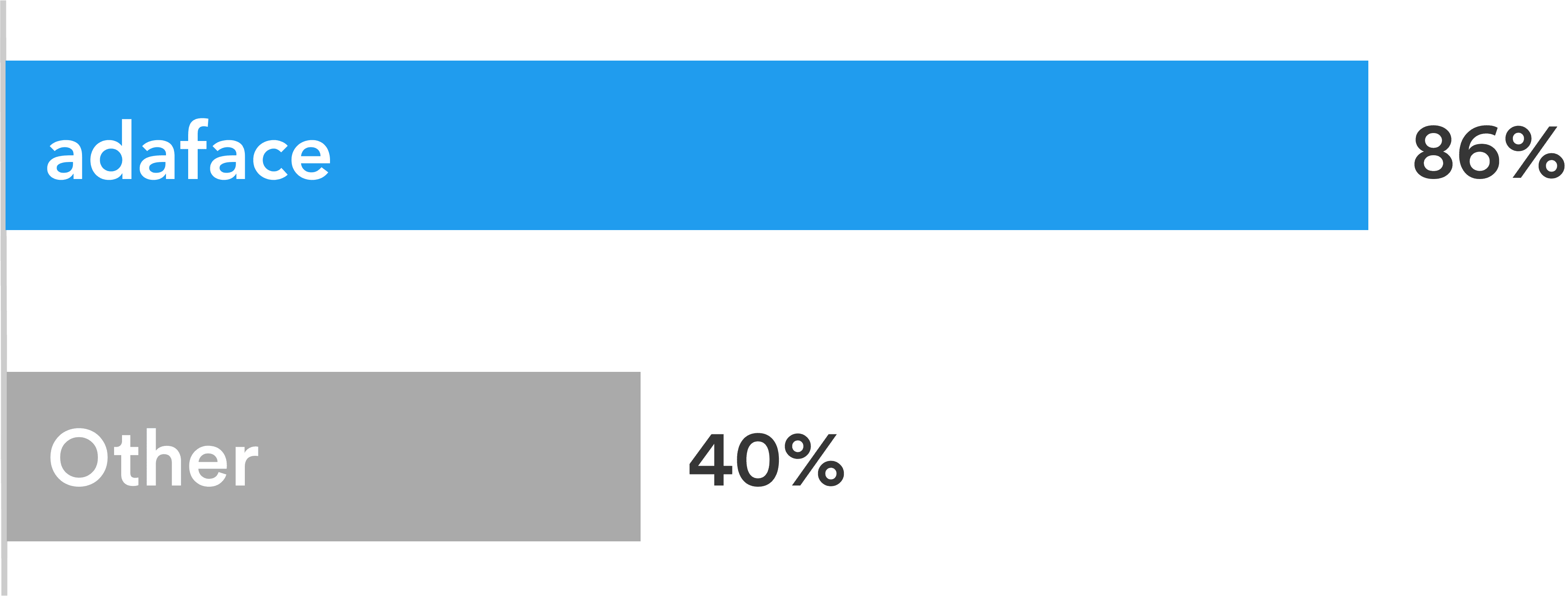
Adaface tests are conversational, low-stress, and take just 25-40 mins to complete.
This is why Adaface has the highest test-completion rate (86%), which is more than 2x better than traditional assessments.
ChatGPT protection
Screen proctoring
Plagiarism detection
Non-googleable questions
User authentication
IP proctoring
Web proctoring
Webcam proctoring
Full screen proctoring
Copy paste protection
Os gerentes de contratação sentiram que, por meio das perguntas técnicas feitas durante as entrevistas do painel, foram capazes de dizer quais candidatos tiveram melhores pontuações e diferenciaram aqueles que não tiveram pontuações tão boas. Eles são altamente satisfeito com a qualidade dos candidatos selecionados na triagem Adaface.
Sim absolutamente. As avaliações personalizadas são configuradas com base na descrição do seu trabalho e incluirão perguntas sobre todas as habilidades obrigatórias que você especificar.
Temos os seguintes recursos anti-trapaça:
Leia mais sobre os Recursos de Proctoring.
O principal a ter em mente é que uma avaliação é uma ferramenta de eliminação, não uma ferramenta de seleção. Uma avaliação de habilidades é otimizada para ajudá -lo a eliminar os candidatos que não são tecnicamente qualificados para o papel, não é otimizado para ajudá -lo a encontrar o melhor candidato para o papel. Portanto, a maneira ideal de usar uma avaliação é decidir uma pontuação limite (normalmente 55%, ajudamos você a comparar) e convidar todos os candidatos que pontuam acima do limiar para as próximas rodadas da entrevista.
Cada avaliação do Adaface é personalizada para a descrição do seu trabalho/ persona do candidato ideal (nossos especialistas no assunto escolherão as perguntas certas para sua avaliação de nossa biblioteca de mais de 10000 perguntas). Esta avaliação pode ser personalizada para qualquer nível de experiência.
Sim, facilita muito a comparação de candidatos. As opções para perguntas do MCQ e a ordem das perguntas são randomizadas. Recursos anti-traking/proctoring no local. Em nosso plano corporativo, também temos a opção de criar várias versões da mesma avaliação com questões de níveis de dificuldade semelhantes.
Não. Infelizmente, não apoiamos os testes práticos no momento. No entanto, você pode usar nossas perguntas de amostra para prática.
Você pode conferir nossos planos de preços.
Sim, você pode se inscrever gratuitamente e visualizar este teste.
Aqui está um guia rápido sobre Como solicitar uma avaliação personalizada no Adaface.