Test Duration
~ 40 min
Difficulty Level
Moderate
Questions
- 5 Ethical Hacking MCQs
- 5 Cybersikkerhed MCQs
- 5 Computernetværk MCQs
Availability
Available on request
About the test:
Den etiske hacking -test evaluerer en kandidats viden og færdigheder inden for etisk hacking med fokus på emner som cybersikkerhed, netværkssikkerhed, webapplikationssikkerhed og trådløs sikkerhed. Testen vurderer kandidatens evne til at identificere sårbarheder, udnytte sikkerhedsfejl og give effektive løsninger for at forhindre uautoriseret adgang og beskytte følsomme oplysninger.
Covered skills:
Test Duration
~ 40 min
Difficulty Level
Moderate
Questions
Availability
Available on request
The Ethical Hacking Test helps recruiters and hiring managers identify qualified candidates from a pool of resumes, and helps in taking objective hiring decisions. It reduces the administrative overhead of interviewing too many candidates and saves time by filtering out unqualified candidates at the first step of the hiring process.
The test screens for the following skills that hiring managers look for in candidates:
Traditional assessment tools use trick questions and puzzles for the screening, which creates a lot of frustration among candidates about having to go through irrelevant screening assessments.
The main reason we started Adaface is that traditional pre-employment assessment platforms are not a fair way for companies to evaluate candidates. At Adaface, our mission is to help companies find great candidates by assessing on-the-job skills required for a role.
Why we started AdafaceWe have a very high focus on the quality of questions that test for on-the-job skills. Every question is non-googleable and we have a very high bar for the level of subject matter experts we onboard to create these questions. We have crawlers to check if any of the questions are leaked online. If/ when a question gets leaked, we get an alert. We change the question for you & let you know.
How we design questionsDette er kun en lille prøve fra vores bibliotek med 10.000+ spørgsmål. De faktiske spørgsmål om dette Etisk hacking -test vil være ikke-gåbart.
| 🧐 Question | |||||
|---|---|---|---|---|---|
Medium Cookie Security Analysis | Solve | ||||
Medium Security Incident | Solve | ||||
Medium Network Traffic Anomaly | Solve | ||||
Medium SQL Log Analysis | Solve | ||||
Medium Misappropriation Post-Migration | Solve | ||||
Medium Mac address and IP on router hop | Solve | ||||
Easy MX Record, DMARC and Email Authentication | Solve | ||||
Medium Remote network resources | Solve | ||||
Medium SSL Certificate Expiry | Solve | ||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
Medium Cookie Security Analysis | 2 mins Cyber Security | Solve | |
Medium Security Incident | 2 mins Cyber Security | Solve | |
Medium Network Traffic Anomaly | 2 mins Cyber Security | Solve | |
Medium SQL Log Analysis | 2 mins Cyber Security | Solve | |
Medium Misappropriation Post-Migration | 3 mins Cyber Security | Solve | |
Medium Mac address and IP on router hop | 2 mins Computer Networks | Solve | |
Easy MX Record, DMARC and Email Authentication | 2 mins Computer Networks | Solve | |
Medium Remote network resources | 3 mins Computer Networks | Solve | |
Medium SSL Certificate Expiry | 2 mins Computer Networks | Solve |
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
Cookie Security Analysis | Cyber Security | Medium | 2 mins | Solve | |
Security Incident | Cyber Security | Medium | 2 mins | Solve | |
Network Traffic Anomaly | Cyber Security | Medium | 2 mins | Solve | |
SQL Log Analysis | Cyber Security | Medium | 2 mins | Solve | |
Misappropriation Post-Migration | Cyber Security | Medium | 3 mins | Solve | |
Mac address and IP on router hop | Computer Networks | Medium | 2 mins | Solve | |
MX Record, DMARC and Email Authentication | Computer Networks | Easy | 2 mins | Solve | |
Remote network resources | Computer Networks | Medium | 3 mins | Solve | |
SSL Certificate Expiry | Computer Networks | Medium | 2 mins | Solve |
Med Adaface var vi i stand til at optimere vores indledende screeningsproces med op mod 75 %, hvilket frigjorde kostbar tid for både ansættelsesledere og vores talentanskaffelsesteam!
Brandon Lee, Leder af mennesker, Love, Bonito
The most important thing while implementing the pre-employment Etisk hacking -test in your hiring process is that it is an elimination tool, not a selection tool. In other words: you want to use the test to eliminate the candidates who do poorly on the test, not to select the candidates who come out at the top. While they are super valuable, pre-employment tests do not paint the entire picture of a candidate’s abilities, knowledge, and motivations. Multiple easy questions are more predictive of a candidate's ability than fewer hard questions. Harder questions are often "trick" based questions, which do not provide any meaningful signal about the candidate's skillset.
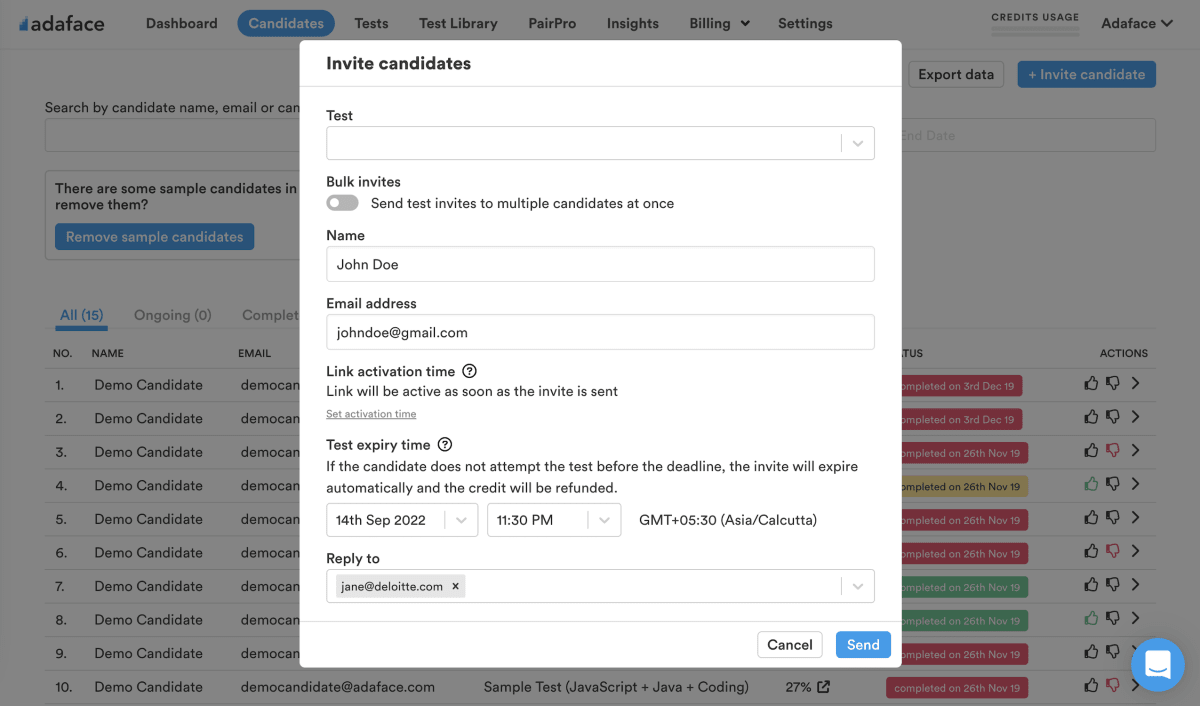
Science behind Adaface testsEmail invites: You can send candidates an email invite to the Etisk hacking -test from your dashboard by entering their email address.
Public link: You can create a public link for each test that you can share with candidates.
API or integrations: You can invite candidates directly from your ATS by using our pre-built integrations with popular ATS systems or building a custom integration with your in-house ATS.
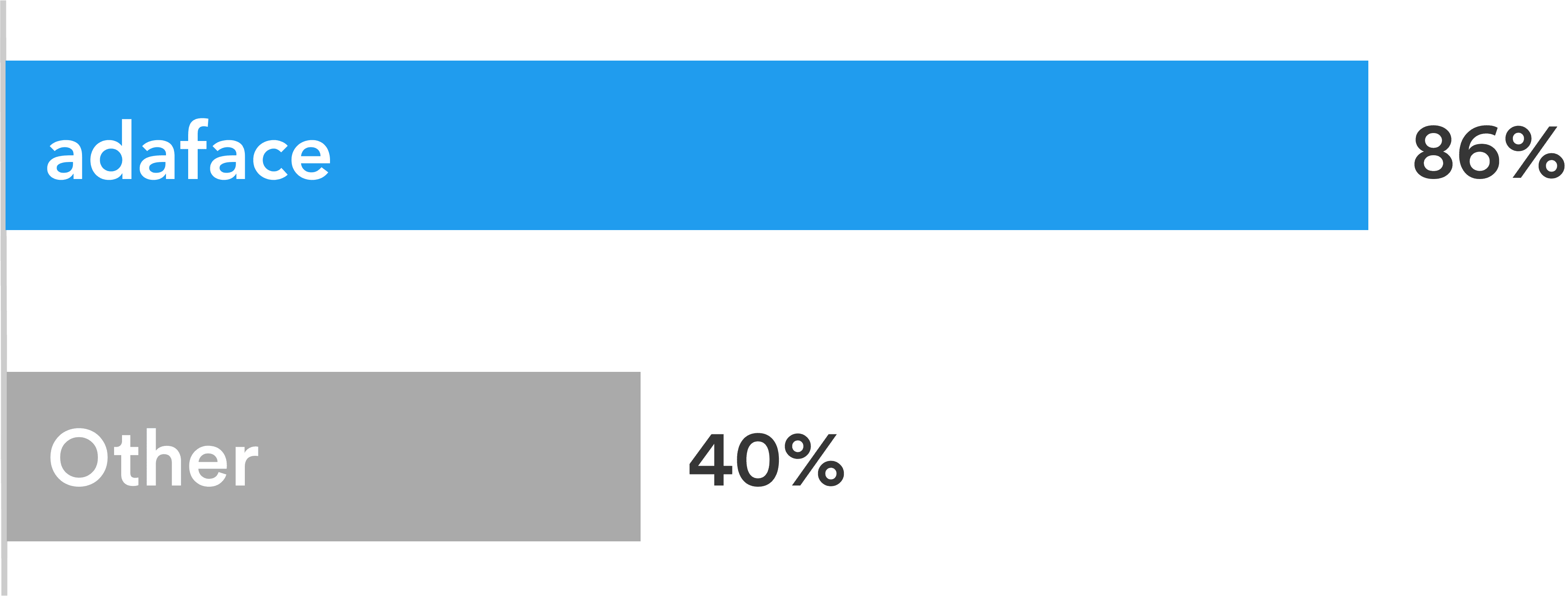
Adaface tests are conversational, low-stress, and take just 25-40 mins to complete.
This is why Adaface has the highest test-completion rate (86%), which is more than 2x better than traditional assessments.
ChatGPT protection
Screen proctoring
Plagiarism detection
Non-googleable questions
User authentication
IP proctoring
Web proctoring
Webcam proctoring
Full screen proctoring
Copy paste protection
Ansættelseslederne mente, at de gennem de tekniske spørgsmål, som de stillede under panelinterviewene, var i stand til at fortælle, hvilke kandidater der havde bedre score og differentieret sig med dem, der ikke scorede så godt. De er meget tilfreds med kvaliteten af de kandidater, der er nomineret med Adaface-screeningen.
Ja absolut. Brugerdefinerede vurderinger er oprettet baseret på din jobbeskrivelse og vil omfatte spørgsmål om alle must-have-færdigheder, du angiver.
Vi har følgende anti-cheating-funktioner på plads:
Læs mere om Proctoring Features.
Den primære ting at huske på er, at en vurdering er et elimineringsværktøj, ikke et udvælgelsesværktøj. En færdighedsvurdering er optimeret for at hjælpe dig med at eliminere kandidater, der ikke er teknisk kvalificerede til rollen, den er ikke optimeret til at hjælpe dig med at finde den bedste kandidat til rollen. Så den ideelle måde at bruge en vurdering på er at beslutte en tærskelværdi (typisk 55%, vi hjælper dig med benchmark) og inviterer alle kandidater, der scorer over tærsklen for de næste interviewrunder.
Hver Adaface -vurdering tilpasses til din jobbeskrivelse/ ideel kandidatperson (vores emneeksperter vælger de rigtige spørgsmål til din vurdering fra vores bibliotek på 10000+ spørgsmål). Denne vurdering kan tilpasses til ethvert erfaringsniveau.
Ja, det gør det meget lettere for dig at sammenligne kandidater. Valgmuligheder for MCQ -spørgsmål og rækkefølgen af spørgsmål randomiseres. Vi har anti-cheating/proctoring funktioner på plads. I vores virksomhedsplan har vi også muligheden for at oprette flere versioner af den samme vurdering med spørgsmål om lignende vanskelighedsniveauer.
Nej. Desværre understøtter vi ikke praksisforsøg i øjeblikket. Du kan dog bruge vores eksempler på spørgsmål til praksis.
Du kan tjekke vores prisplaner.
Ja, du kan tilmelde dig gratis og forhåndsvise denne test.
Her er en hurtig guide til hvordan man anmoder om en brugerdefineret vurdering på adaface.