Test Duration
~ 30 Min
Difficulty Level
Moderate
Questions
- 4 Data Structures MCQs
- 4 Attitudine tecnica MCQs
- 4 Operating System MCQs
- 4 System Design MCQs
- 4 Reti di computer MCQs
Availability
Available on request
About the test:
Il test dell'architettura dei sistemi informatici valuta la comprensione di un candidato della struttura, dell'organizzazione e del comportamento del sistema informatico, inclusi argomenti come l'architettura del processore, la gerarchia della memoria, i sistemi di input/output e le prestazioni del sistema. Valuta anche la conoscenza delle strutture di dati e dei principi di ingegneria del software.
Covered skills:
Test Duration
~ 30 Min
Difficulty Level
Moderate
Questions
Availability
Available on request
The Computer Systems Architecture Test helps recruiters and hiring managers identify qualified candidates from a pool of resumes, and helps in taking objective hiring decisions. It reduces the administrative overhead of interviewing too many candidates and saves time by filtering out unqualified candidates at the first step of the hiring process.
The test screens for the following skills that hiring managers look for in candidates:
Traditional assessment tools use trick questions and puzzles for the screening, which creates a lot of frustration among candidates about having to go through irrelevant screening assessments.
The main reason we started Adaface is that traditional pre-employment assessment platforms are not a fair way for companies to evaluate candidates. At Adaface, our mission is to help companies find great candidates by assessing on-the-job skills required for a role.
Why we started AdafaceWe have a very high focus on the quality of questions that test for on-the-job skills. Every question is non-googleable and we have a very high bar for the level of subject matter experts we onboard to create these questions. We have crawlers to check if any of the questions are leaked online. If/ when a question gets leaked, we get an alert. We change the question for you & let you know.
How we design questionsQuesti sono solo un piccolo campione della nostra biblioteca di oltre 10.000 domande. Le domande reali su questo Test dell'architettura dei sistemi informatici sarà non googleabile.
| 🧐 Question | |||||
|---|---|---|---|---|---|
Hard Graph Traversal and Data Storage | Solve | ||||
Medium Implementing a Browser's Back Button | Solve | ||||
Easy Linked List Element Removal | Solve | ||||
Medium Decryptor | Solve | ||||
Hard Fibonacci codes | Solve | ||||
Hard Palindrome Test cases | Solve | ||||
Medium Rewards Activities Order | Solve | ||||
Medium Optimal Data Replication and Consistency in Distributed Systems | Solve | ||||
Easy Real-time Vehicle Tracking for Logistics Company | Solve | ||||
Medium Session stickiness with ELB | Solve | ||||
Medium Updating UI after Encoding | Solve | ||||
Medium Mac address and IP on router hop | Solve | ||||
Easy MX Record, DMARC and Email Authentication | Solve | ||||
Medium Remote network resources | Solve | ||||
Medium SSL Certificate Expiry | Solve | ||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
Hard Graph Traversal and Data Storage | 3 mins Data Structures | Solve | |
Medium Implementing a Browser's Back Button | 2 mins Data Structures | Solve | |
Easy Linked List Element Removal | 2 mins Data Structures | Solve | |
Medium Decryptor | 2 mins Technical Aptitude | Solve | |
Hard Fibonacci codes | 2 mins Technical Aptitude | Solve | |
Hard Palindrome Test cases | 2 mins Technical Aptitude | Solve | |
Medium Rewards Activities Order | 3 mins Technical Aptitude | Solve | |
Medium Optimal Data Replication and Consistency in Distributed Systems | 2 mins System Design | Solve | |
Easy Real-time Vehicle Tracking for Logistics Company | 2 mins System Design | Solve | |
Medium Session stickiness with ELB | 2 mins System Design | Solve | |
Medium Updating UI after Encoding | 2 mins System Design | Solve | |
Medium Mac address and IP on router hop | 2 mins Computer Networks | Solve | |
Easy MX Record, DMARC and Email Authentication | 2 mins Computer Networks | Solve | |
Medium Remote network resources | 3 mins Computer Networks | Solve | |
Medium SSL Certificate Expiry | 2 mins Computer Networks | Solve |
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
Graph Traversal and Data Storage | Data Structures | Hard | 3 mins | Solve | |
Implementing a Browser's Back Button | Data Structures | Medium | 2 mins | Solve | |
Linked List Element Removal | Data Structures | Easy | 2 mins | Solve | |
Decryptor | Technical Aptitude | Medium | 2 mins | Solve | |
Fibonacci codes | Technical Aptitude | Hard | 2 mins | Solve | |
Palindrome Test cases | Technical Aptitude | Hard | 2 mins | Solve | |
Rewards Activities Order | Technical Aptitude | Medium | 3 mins | Solve | |
Optimal Data Replication and Consistency in Distributed Systems | System Design | Medium | 2 mins | Solve | |
Real-time Vehicle Tracking for Logistics Company | System Design | Easy | 2 mins | Solve | |
Session stickiness with ELB | System Design | Medium | 2 mins | Solve | |
Updating UI after Encoding | System Design | Medium | 2 mins | Solve | |
Mac address and IP on router hop | Computer Networks | Medium | 2 mins | Solve | |
MX Record, DMARC and Email Authentication | Computer Networks | Easy | 2 mins | Solve | |
Remote network resources | Computer Networks | Medium | 3 mins | Solve | |
SSL Certificate Expiry | Computer Networks | Medium | 2 mins | Solve |
Con Adaface siamo stati in grado di ottimizzare il nostro processo di screening iniziale fino al 75%, liberando tempo prezioso sia per i responsabili delle assunzioni che per il nostro team di acquisizione dei talenti!
Brandon Lee, Capo del Popolo, Love, Bonito
The most important thing while implementing the pre-employment Test dell'architettura dei sistemi informatici in your hiring process is that it is an elimination tool, not a selection tool. In other words: you want to use the test to eliminate the candidates who do poorly on the test, not to select the candidates who come out at the top. While they are super valuable, pre-employment tests do not paint the entire picture of a candidate’s abilities, knowledge, and motivations. Multiple easy questions are more predictive of a candidate's ability than fewer hard questions. Harder questions are often "trick" based questions, which do not provide any meaningful signal about the candidate's skillset.
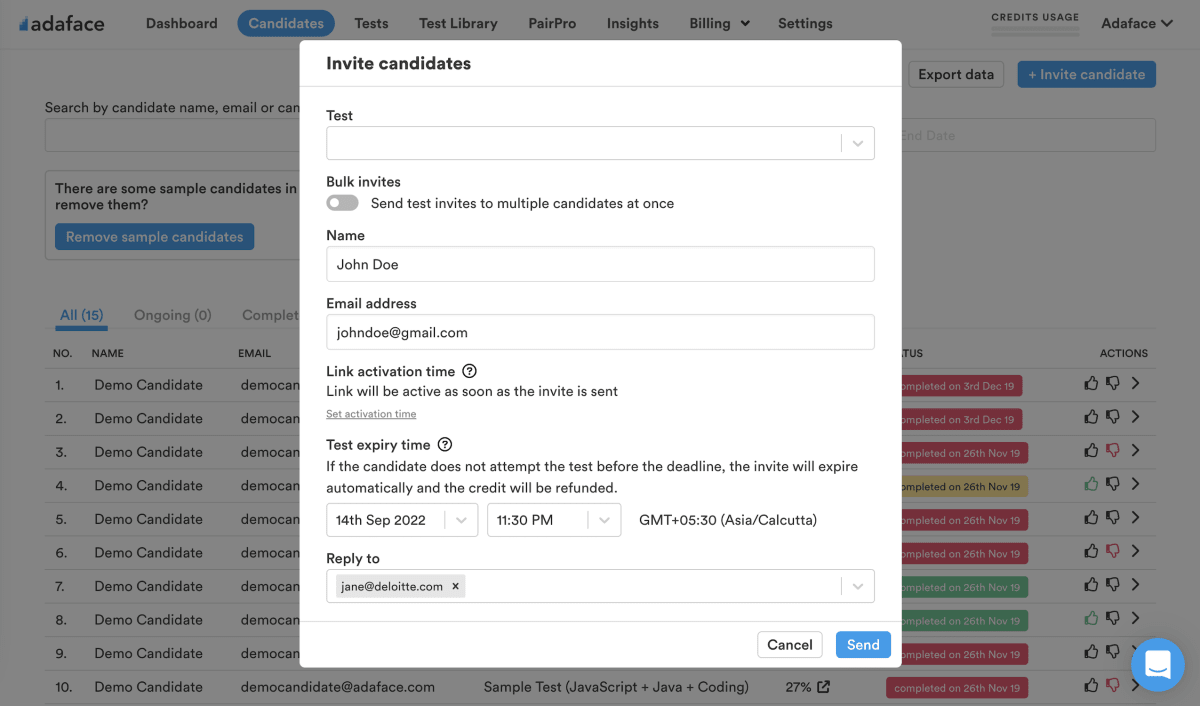
Science behind Adaface testsEmail invites: You can send candidates an email invite to the Test dell'architettura dei sistemi informatici from your dashboard by entering their email address.
Public link: You can create a public link for each test that you can share with candidates.
API or integrations: You can invite candidates directly from your ATS by using our pre-built integrations with popular ATS systems or building a custom integration with your in-house ATS.
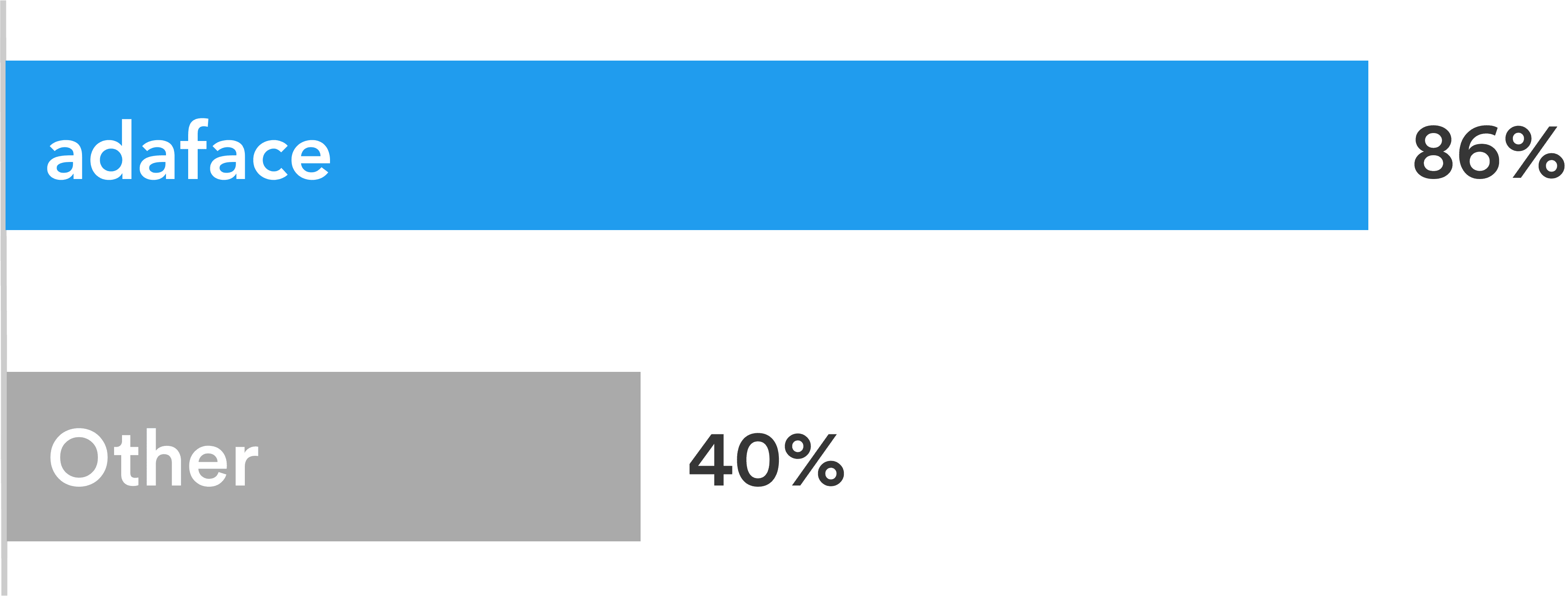
Adaface tests are conversational, low-stress, and take just 25-40 mins to complete.
This is why Adaface has the highest test-completion rate (86%), which is more than 2x better than traditional assessments.
ChatGPT protection
Screen proctoring
Plagiarism detection
Non-googleable questions
User authentication
IP proctoring
Web proctoring
Webcam proctoring
Full screen proctoring
Copy paste protection
I responsabili delle assunzioni hanno ritenuto che, attraverso le domande tecniche poste durante le interviste del panel, erano in grado di individuare quali candidati avevano ottenuto i punteggi migliori e di differenziarli da quelli che non avevano ottenuto altrettanto punteggio. Sono altamente soddisfatto con la qualità dei candidati selezionati con lo screening Adaface.
Si assolutamente. Le valutazioni personalizzate sono impostate in base alla descrizione del tuo lavoro e includeranno domande su tutte le competenze indispensabili che specificate.
Abbiamo in atto le seguenti caratteristiche anti-cheat:
Leggi di più sulle caratteristiche di procuratore.
La cosa principale da tenere a mente è che una valutazione è uno strumento di eliminazione, non uno strumento di selezione. Una valutazione delle competenze è ottimizzata per aiutarti a eliminare i candidati che non sono tecnicamente qualificati per il ruolo, non è ottimizzato per aiutarti a trovare il miglior candidato per il ruolo. Quindi il modo ideale per utilizzare una valutazione è decidere un punteggio di soglia (in genere il 55%, ti aiutiamo a benchmark) e invitiamo tutti i candidati che segnano al di sopra della soglia per i prossimi round di intervista.
Ogni valutazione di Adaface è personalizzata per la descrizione del tuo lavoro/ personaggio del candidato ideale (i nostri esperti in materia sceglieranno le domande giuste per la tua valutazione dalla nostra biblioteca di oltre 10000 domande). Questa valutazione può essere personalizzata per qualsiasi livello di esperienza.
Sì, ti rende molto più facile confrontare i candidati. Le opzioni per le domande MCQ e l'ordine delle domande sono randomizzate. Abbiamo anti-cheatri/procuratore in atto. Nel nostro piano aziendale, abbiamo anche la possibilità di creare più versioni della stessa valutazione con questioni di difficoltà simili.
No. Sfortunatamente, al momento non supportiamo i test di pratica. Tuttavia, è possibile utilizzare le nostre domande di esempio per la pratica.
Puoi controllare i nostri piani di prezzo.
Sì, puoi iscriverti gratuitamente e visualizzare in anteprima questo test.
Ecco una rapida guida su come richiedere una valutazione personalizzata su Adaface.