Test Duration
~ 30 min
Difficulty Level
Moderate
Questions
- 4 Data Structures MCQs
- 4 Technische bekwaamheid MCQs
- 4 Operating System MCQs
- 4 System Design MCQs
- 4 Computer netwerken MCQs
Availability
Available on request
About the test:
De Computer Systems -architectuurtest evalueert het begrip van een kandidaat van de structuur, organisatie en gedrag van een computersysteem, inclusief onderwerpen zoals processorarchitectuur, geheugenhiërarchie, input/output -systemen en systeemprestaties. Het beoordeelt ook kennis van gegevensstructuren en software -engineeringprincipes.
Covered skills:
Test Duration
~ 30 min
Difficulty Level
Moderate
Questions
Availability
Available on request
The Computer Systems Architecture Test helps recruiters and hiring managers identify qualified candidates from a pool of resumes, and helps in taking objective hiring decisions. It reduces the administrative overhead of interviewing too many candidates and saves time by filtering out unqualified candidates at the first step of the hiring process.
The test screens for the following skills that hiring managers look for in candidates:
Traditional assessment tools use trick questions and puzzles for the screening, which creates a lot of frustration among candidates about having to go through irrelevant screening assessments.
The main reason we started Adaface is that traditional pre-employment assessment platforms are not a fair way for companies to evaluate candidates. At Adaface, our mission is to help companies find great candidates by assessing on-the-job skills required for a role.
Why we started AdafaceWe have a very high focus on the quality of questions that test for on-the-job skills. Every question is non-googleable and we have a very high bar for the level of subject matter experts we onboard to create these questions. We have crawlers to check if any of the questions are leaked online. If/ when a question gets leaked, we get an alert. We change the question for you & let you know.
How we design questionsDit zijn slechts een klein monster uit onze bibliotheek met meer dan 10.000 vragen. De werkelijke vragen hierover Computersystemen architectuurtest zal niet-googelbaar zijn.
| 🧐 Question | |||||
|---|---|---|---|---|---|
Hard Graph Traversal and Data Storage | Solve | ||||
Medium Implementing a Browser's Back Button | Solve | ||||
Easy Linked List Element Removal | Solve | ||||
Medium Decryptor | Solve | ||||
Hard Fibonacci codes | Solve | ||||
Hard Palindrome Test cases | Solve | ||||
Medium Rewards Activities Order | Solve | ||||
Medium Optimal Data Replication and Consistency in Distributed Systems | Solve | ||||
Easy Real-time Vehicle Tracking for Logistics Company | Solve | ||||
Medium Session stickiness with ELB | Solve | ||||
Medium Updating UI after Encoding | Solve | ||||
Medium Mac address and IP on router hop | Solve | ||||
Easy MX Record, DMARC and Email Authentication | Solve | ||||
Medium Remote network resources | Solve | ||||
Medium SSL Certificate Expiry | Solve | ||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
Hard Graph Traversal and Data Storage | 3 mins Data Structures | Solve | |
Medium Implementing a Browser's Back Button | 2 mins Data Structures | Solve | |
Easy Linked List Element Removal | 2 mins Data Structures | Solve | |
Medium Decryptor | 2 mins Technical Aptitude | Solve | |
Hard Fibonacci codes | 2 mins Technical Aptitude | Solve | |
Hard Palindrome Test cases | 2 mins Technical Aptitude | Solve | |
Medium Rewards Activities Order | 3 mins Technical Aptitude | Solve | |
Medium Optimal Data Replication and Consistency in Distributed Systems | 2 mins System Design | Solve | |
Easy Real-time Vehicle Tracking for Logistics Company | 2 mins System Design | Solve | |
Medium Session stickiness with ELB | 2 mins System Design | Solve | |
Medium Updating UI after Encoding | 2 mins System Design | Solve | |
Medium Mac address and IP on router hop | 2 mins Computer Networks | Solve | |
Easy MX Record, DMARC and Email Authentication | 2 mins Computer Networks | Solve | |
Medium Remote network resources | 3 mins Computer Networks | Solve | |
Medium SSL Certificate Expiry | 2 mins Computer Networks | Solve |
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
Graph Traversal and Data Storage | Data Structures | Hard | 3 mins | Solve | |
Implementing a Browser's Back Button | Data Structures | Medium | 2 mins | Solve | |
Linked List Element Removal | Data Structures | Easy | 2 mins | Solve | |
Decryptor | Technical Aptitude | Medium | 2 mins | Solve | |
Fibonacci codes | Technical Aptitude | Hard | 2 mins | Solve | |
Palindrome Test cases | Technical Aptitude | Hard | 2 mins | Solve | |
Rewards Activities Order | Technical Aptitude | Medium | 3 mins | Solve | |
Optimal Data Replication and Consistency in Distributed Systems | System Design | Medium | 2 mins | Solve | |
Real-time Vehicle Tracking for Logistics Company | System Design | Easy | 2 mins | Solve | |
Session stickiness with ELB | System Design | Medium | 2 mins | Solve | |
Updating UI after Encoding | System Design | Medium | 2 mins | Solve | |
Mac address and IP on router hop | Computer Networks | Medium | 2 mins | Solve | |
MX Record, DMARC and Email Authentication | Computer Networks | Easy | 2 mins | Solve | |
Remote network resources | Computer Networks | Medium | 3 mins | Solve | |
SSL Certificate Expiry | Computer Networks | Medium | 2 mins | Solve |
Met Adaface konden we ons eerste screeningproces met ruim 75% optimaliseren, waardoor kostbare tijd vrijkwam voor zowel de rekruteringsmanagers als ons talentacquisitieteam!
Brandon Lee, Hoofd Mensen, Love, Bonito
The most important thing while implementing the pre-employment Computersystemen architectuurtest in your hiring process is that it is an elimination tool, not a selection tool. In other words: you want to use the test to eliminate the candidates who do poorly on the test, not to select the candidates who come out at the top. While they are super valuable, pre-employment tests do not paint the entire picture of a candidate’s abilities, knowledge, and motivations. Multiple easy questions are more predictive of a candidate's ability than fewer hard questions. Harder questions are often "trick" based questions, which do not provide any meaningful signal about the candidate's skillset.
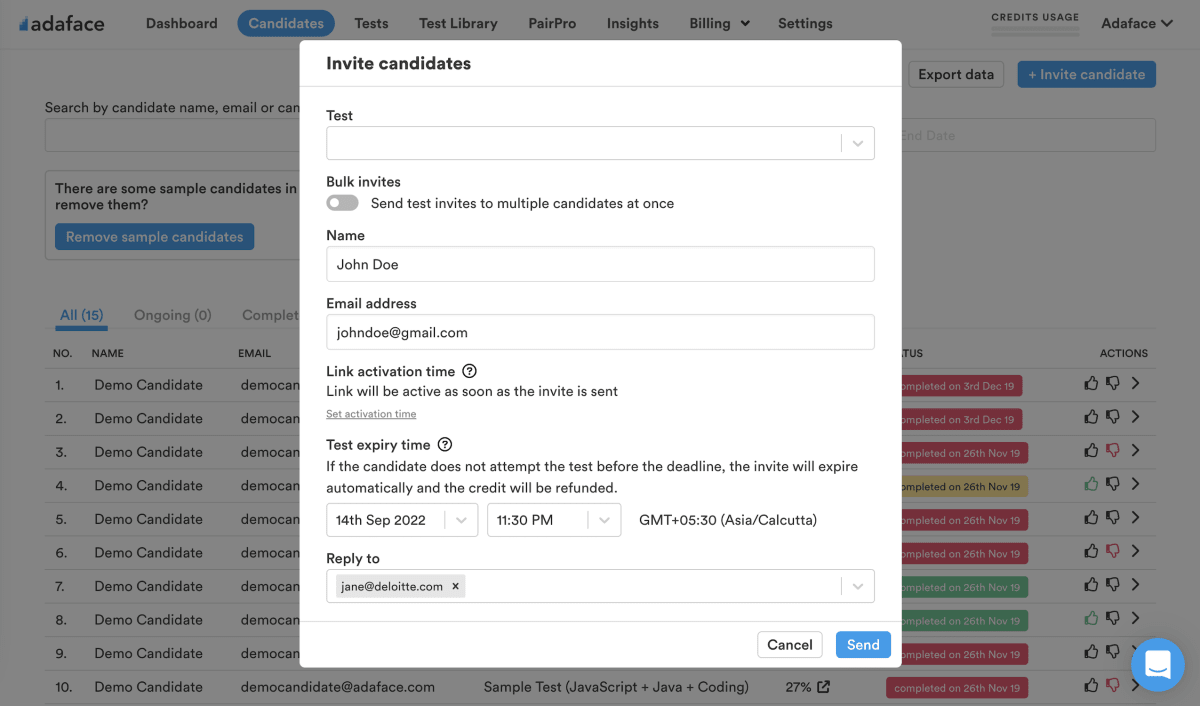
Science behind Adaface testsEmail invites: You can send candidates an email invite to the Computersystemen architectuurtest from your dashboard by entering their email address.
Public link: You can create a public link for each test that you can share with candidates.
API or integrations: You can invite candidates directly from your ATS by using our pre-built integrations with popular ATS systems or building a custom integration with your in-house ATS.
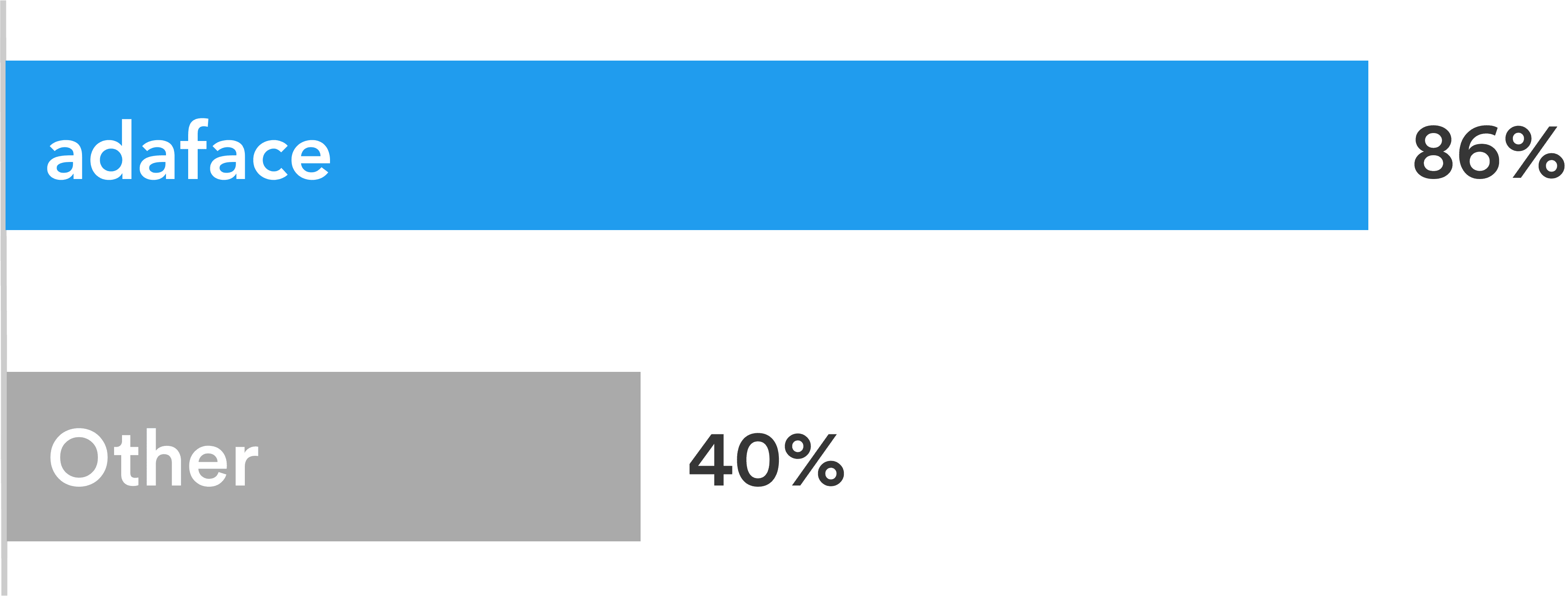
Adaface tests are conversational, low-stress, and take just 25-40 mins to complete.
This is why Adaface has the highest test-completion rate (86%), which is more than 2x better than traditional assessments.
ChatGPT protection
Screen proctoring
Plagiarism detection
Non-googleable questions
User authentication
IP proctoring
Web proctoring
Webcam proctoring
Full screen proctoring
Copy paste protection
De rekruteringsmanagers waren van mening dat ze door de technische vragen die ze tijdens de panelgesprekken stelden, konden zien welke kandidaten beter scoorden, en onderscheidden ze zich met degenen die niet zo goed scoorden. Zij zijn zeer tevreden met de kwaliteit van de kandidaten op de shortlist van de Adaface-screening.
Ja absoluut. Aangepaste beoordelingen zijn opgezet op basis van uw functiebeschrijving en bevatten vragen over alle must-have vaardigheden die u opgeeft.
We hebben de volgende anti-cheating-functies op zijn plaats:
Lees meer over de Proctoring -functies.
Het belangrijkste om in gedachten te houden is dat een beoordeling een eliminatietool is, geen selectietool. Een vaardighedenbeoordeling is geoptimaliseerd om u te helpen kandidaten te elimineren die niet technisch gekwalificeerd zijn voor de rol, het is niet geoptimaliseerd om u te helpen de beste kandidaat voor de rol te vinden. Dus de ideale manier om een beoordeling te gebruiken is om een drempelscore te bepalen (meestal 55%, wij helpen u benchmark) en alle kandidaten uit te nodigen die boven de drempel scoren voor de volgende interviewrondes.
Elke ADAFACE -beoordeling is aangepast aan uw functiebeschrijving/ ideale kandidaatpersonage (onze experts van het onderwerp zullen de juiste vragen kiezen voor uw beoordeling uit onze bibliotheek van 10000+ vragen). Deze beoordeling kan worden aangepast voor elk ervaringsniveau.
Ja, het maakt het veel gemakkelijker voor u om kandidaten te vergelijken. Opties voor MCQ -vragen en de volgorde van vragen worden gerandomiseerd. We hebben anti-cheating/proctoring functies. In ons bedrijfsplan hebben we ook de optie om meerdere versies van dezelfde beoordeling te maken met vragen over vergelijkbare moeilijkheidsniveaus.
Nee. Helaas ondersteunen we op dit moment geen oefentests. U kunt echter onze voorbeeldvragen gebruiken voor praktijk.
U kunt onze [prijsplannen] bekijken (https://www.adaface.com/pricing/).
Ja, u kunt gratis aanmelden en een voorbeeld van deze test.
Hier is een korte handleiding over hoe een aangepaste beoordeling aanvragen op Adaface.