Test Duration
40 minsDifficulty Level
Moderate
Questions
- 8 CISCO MCQs
- 4 Computer Networks MCQs
- 4 Cyber Security MCQs
Availability
Ready to useThe Cisco Security Online Test uses scenario-based MCQs to evaluate candidates on their understanding of network security concepts and Cisco network security products and solutions. The test assesses candidates on their knowledge of security technologies, such as firewall, VPN, intrusion prevention, and content security, as well as their ability to design and implement secure network architectures using Cisco products.
Covered skills:
Test Duration
40 minsDifficulty Level
Moderate
Questions
Availability
Ready to useThe CISCO Security Online Test helps recruiters and hiring managers identify qualified candidates from a pool of resumes, and helps in taking objective hiring decisions. It reduces the administrative overhead of interviewing too many candidates and saves time by filtering out unqualified candidates at the first step of the hiring process.
The test screens for the following skills that hiring managers look for in candidates:
Use Adaface tests trusted by recruitment teams globally. Adaface skill assessments measure on-the-job skills of candidates, providing employers with an accurate tool for screening potential hires.
We have a very high focus on the quality of questions that test for on-the-job skills. Every question is non-googleable and we have a very high bar for the level of subject matter experts we onboard to create these questions. We have crawlers to check if any of the questions are leaked online. If/ when a question gets leaked, we get an alert. We change the question for you & let you know.
How we design questionsThese are just a small sample from our library of 15,000+ questions. The actual questions on this CISCO Security Online Test will be non-googleable.
| 🧐 Question | |||||
|---|---|---|---|---|---|
|
Medium
BGP Path Selection
|
Solve
|
||||
|
|
|||||
|
Medium
OSPF Inter-Area Route Filtering
|
Solve
|
||||
|
|
|||||
|
Medium
OSPF Network Analysis
|
Solve
|
||||
|
|
|||||
|
Medium
Routing Protocols Configuration
|
Solve
|
||||
|
|
|||||
|
Medium
Mac address and IP on router hop
|
Solve
|
||||
|
|
|||||
|
Easy
MX Record, DMARC and Email Authentication
|
Solve
|
||||
|
|
|||||
|
Medium
Remote network resources
|
Solve
|
||||
|
|
|||||
|
Medium
SSL Certificate Expiry
|
Solve
|
||||
|
|
|||||
|
Medium
Cookie Security Analysis
|
Solve
|
||||
|
|
|||||
|
Medium
Security Incident
|
Solve
|
||||
|
|
|||||
|
Medium
Network Traffic Anomaly
|
Solve
|
||||
|
|
|||||
|
Medium
SQL Log Analysis
|
Solve
|
||||
|
|
|||||
|
Medium
Misappropriation Post-Migration
|
Solve
|
||||
|
|
|||||
| 🧐 Question | 🔧 Skill | ||
|---|---|---|---|
|
Medium
BGP Path Selection
|
2 mins CISCO
|
Solve
|
|
|
Medium
OSPF Inter-Area Route Filtering
|
3 mins CISCO
|
Solve
|
|
|
Medium
OSPF Network Analysis
|
2 mins CISCO
|
Solve
|
|
|
Medium
Routing Protocols Configuration
|
2 mins CISCO
|
Solve
|
|
|
Medium
Mac address and IP on router hop
|
2 mins Computer Networks
|
Solve
|
|
|
Easy
MX Record, DMARC and Email Authentication
|
2 mins Computer Networks
|
Solve
|
|
|
Medium
Remote network resources
|
3 mins Computer Networks
|
Solve
|
|
|
Medium
SSL Certificate Expiry
|
2 mins Computer Networks
|
Solve
|
|
|
Medium
Cookie Security Analysis
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
Security Incident
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
Network Traffic Anomaly
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
SQL Log Analysis
|
2 mins Cyber Security
|
Solve
|
|
|
Medium
Misappropriation Post-Migration
|
3 mins Cyber Security
|
Solve
|
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
|
BGP Path Selection
|
CISCO
|
Medium | 2 mins |
Solve
|
|
|
OSPF Inter-Area Route Filtering
|
CISCO
|
Medium | 3 mins |
Solve
|
|
|
OSPF Network Analysis
|
CISCO
|
Medium | 2 mins |
Solve
|
|
|
Routing Protocols Configuration
|
CISCO
|
Medium | 2 mins |
Solve
|
|
|
Mac address and IP on router hop
|
Computer Networks
|
Medium | 2 mins |
Solve
|
|
|
MX Record, DMARC and Email Authentication
|
Computer Networks
|
Easy | 2 mins |
Solve
|
|
|
Remote network resources
|
Computer Networks
|
Medium | 3 mins |
Solve
|
|
|
SSL Certificate Expiry
|
Computer Networks
|
Medium | 2 mins |
Solve
|
|
|
Cookie Security Analysis
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
Security Incident
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
Network Traffic Anomaly
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
SQL Log Analysis
|
Cyber Security
|
Medium | 2 mins |
Solve
|
|
|
Misappropriation Post-Migration
|
Cyber Security
|
Medium | 3 mins |
Solve
|
With Adaface, we were able to optimise our initial screening process by upwards of 75%, freeing up precious time for both hiring managers and our talent acquisition team alike!
Brandon Lee, Head of People, Love, Bonito
It's very easy to share assessments with candidates and for candidates to use. We get good feedback from candidates about completing the tests. Adaface are very responsive and friendly to deal with.
Kirsty Wood, Human Resources, WillyWeather
We were able to close 106 positions in a record time of 45 days! Adaface enables us to conduct aptitude and psychometric assessments seamlessly. My hiring managers have never been happier with the quality of candidates shortlisted.
Amit Kataria, CHRO, Hanu
We evaluated several of their competitors and found Adaface to be the most compelling. Great library of questions that are designed to test for fit rather than memorization of algorithms.
Swayam Narain, CTO, Affable
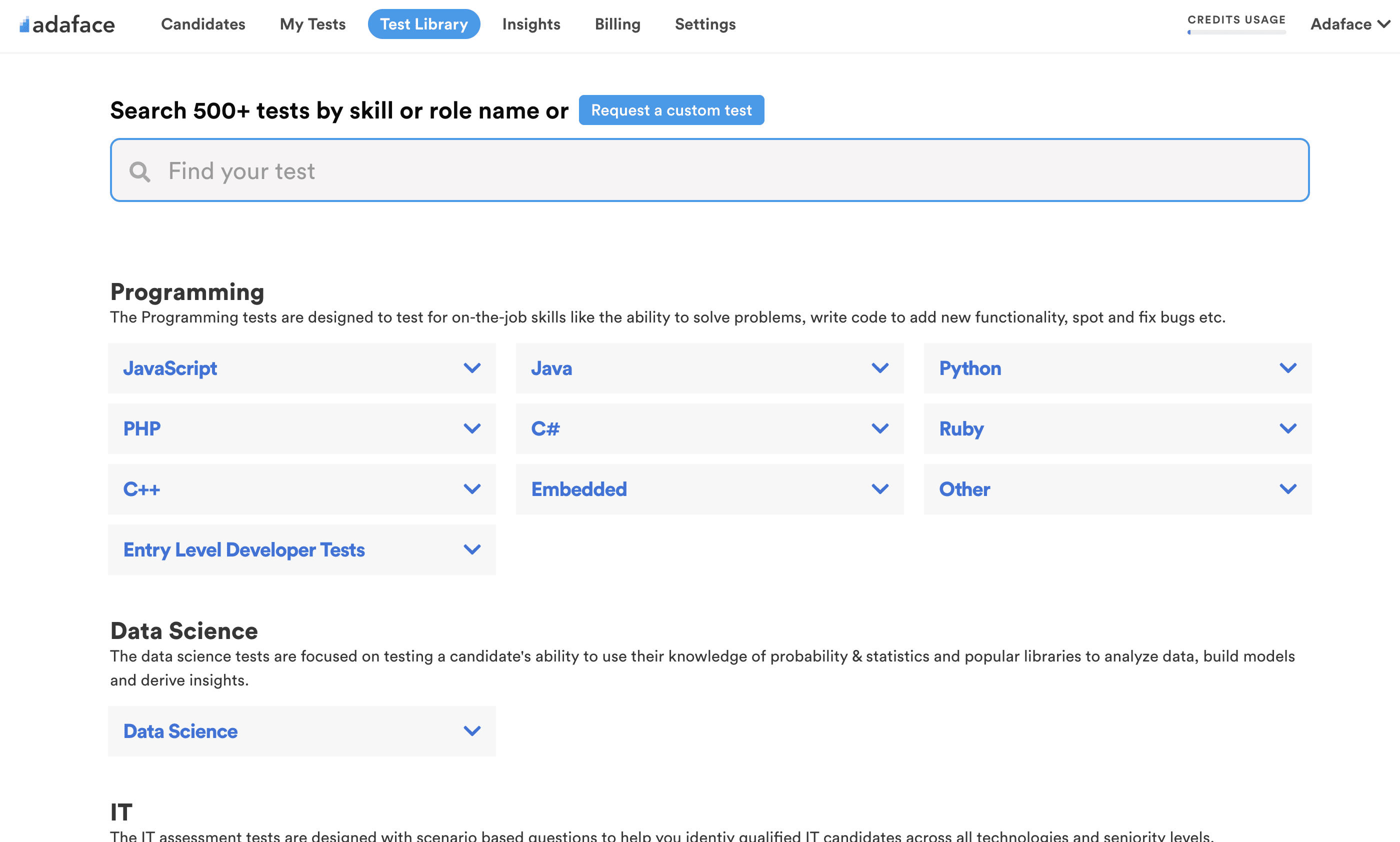
The Adaface test library features 500+ tests to enable you to test candidates on all popular skills- everything from programming languages, software frameworks, devops, logical reasoning, abstract reasoning, critical thinking, fluid intelligence, content marketing, talent acquisition, customer service, accounting, product management, sales and more.
The CISCO Security Online Test is designed to assess the skills and knowledge of professionals in CISCO security technologies. It is used by recruiters to evaluate candidates on their proficiency in network security concepts, CISCO security appliances, and solutions.
Yes, recruiters can request a single custom test with multiple skills. You may consider looking into our Network Engineer Test for more details on how we assess network engineering capabilities.
The test includes 8 multiple-choice questions on CISCO, 4 on computer networks, and 4 on cyber security topics. It covers skills such as CISCO Firewall, CISCO VPN, and network security concepts, making it comprehensive for senior roles.
We recommend using this test as a pre-screening tool at the beginning of your recruitment process. You can add a link to the assessment in your job post or directly invite candidates by email.
Yes, you can test both CISCO security and cyber security together. This combination is beneficial to assess a candidate's overall network security capabilities. Check our Cyber Security Assessment Test for more details.
We offer several security-related tests, including:
Yes, absolutely. Custom assessments are set up based on your job description, and will include questions on all must-have skills you specify. Here's a quick guide on how you can request a custom test.
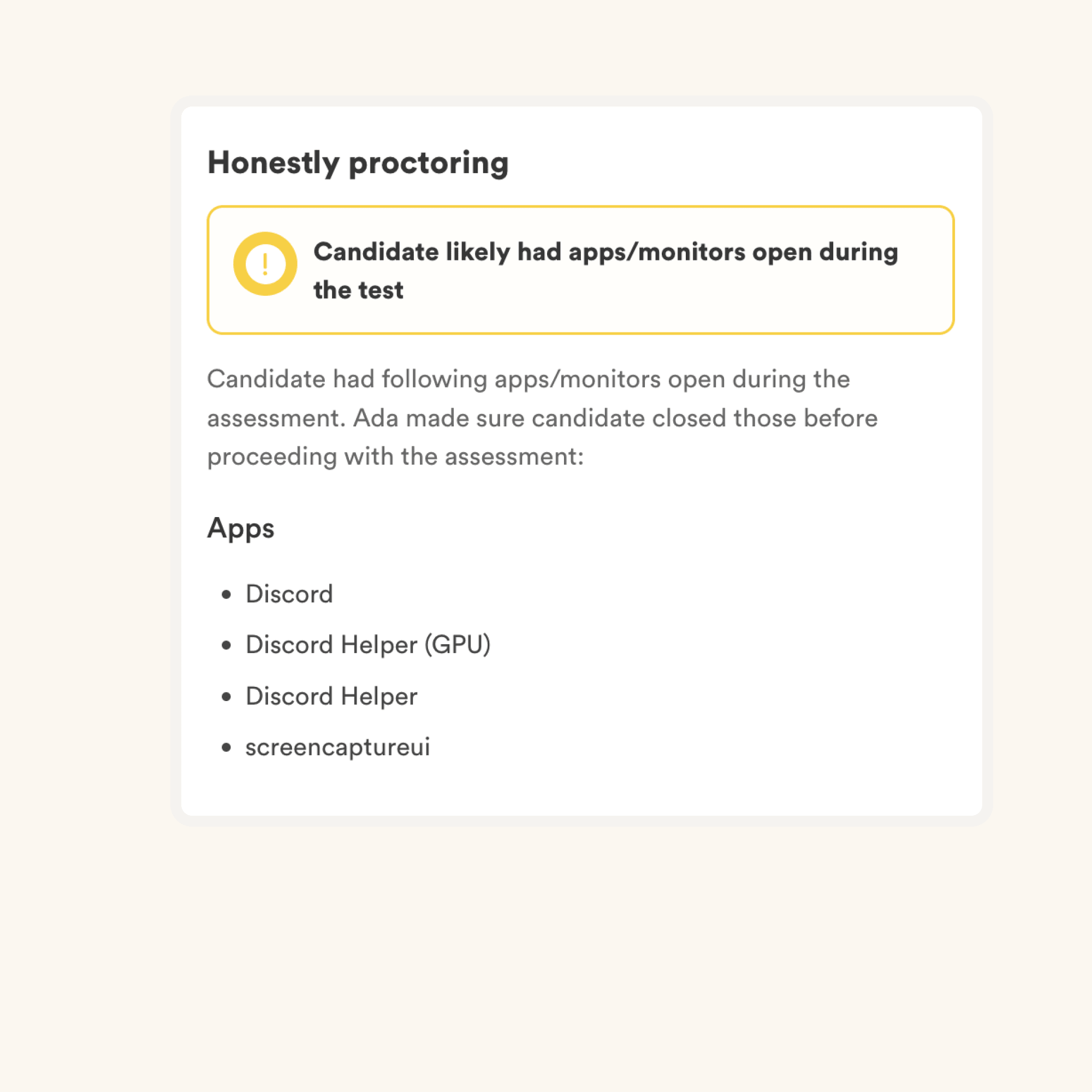
We have the following anti-cheating features in place:
Read more about the proctoring features.
The primary thing to keep in mind is that an assessment is an elimination tool, not a selection tool. A skills assessment is optimized to help you eliminate candidates who are not technically qualified for the role, it is not optimized to help you find the best candidate for the role. So the ideal way to use an assessment is to decide a threshold score (typically 55%, we help you benchmark) and invite all candidates who score above the threshold for the next rounds of interview.
Each Adaface assessment is customized to your job description/ ideal candidate persona (our subject matter experts will pick the right questions for your assessment from our library of 10000+ questions). This assessment can be customized for any experience level.
Yes, it makes it much easier for you to compare candidates. Options for MCQ questions and the order of questions are randomized. We have anti-cheating/ proctoring features in place. In our enterprise plan, we also have the option to create multiple versions of the same assessment with questions of similar difficulty levels.
No. Unfortunately, we do not support practice tests at the moment. However, you can use our sample questions for practice.
You can check out our pricing plans.
Yes, you can sign up for free and preview this test.
Here is a quick guide on how to request a custom assessment on Adaface.