Adaface Sample Cyber Security Questions
Here are some sample Cyber Security questions from our premium questions library (10273 non-googleable questions).
Skills
Programming Languages
Data Science
Frontend
Backend
Software Engineering Basics
Data Engineering
Excel SQL MySQL PostgreSQL Oracle SQL MS SQL MongoDB NoSQL SQLite Data Analysis Data Modeling Firestore Cassandra Tableau Power BI Power Apps Power Automate Terraform Kafka Qlik Sense QlikView SQL Server ETL Data Modeling Data Warehouse Data Mining Oracle RAC Oracle WebCenter Splunk ServiceNow Google Sheets Data Storytelling Data Wrangling
Cloud Engineering
Azure AWS Windows Administration Computer Networks Azure Data Factory Terraform IBM DB2 IBM RPG IBM CL Programming Site Reliability Engineering Technical Support DevOps Cloud Computing IBM FOCUS IBM AIX IBM InfoSphere DataStage IBM DB/400 IBM WebSphere IBM TRIRIGA Jaspersoft Linux Administration F5 Networks Ethical Hacking
Test Engineering
Product
Aptitude
Logical Reasoning Abstract Reasoning English Reading Comprehension Spatial Reasoning Verbal Reasoning Diagrammatic Reasoning Critical Thinking Data Interpretation Situational Judgement Attention to Detail Numerical Reasoning Aptitude Quantitative Reasoning Inductive Reasoning Deductive Reasoning Error Checking Qualitative Aptitude Customer Success
Accounting
Others
Embedded Systems Agile/Scrum Cyber Security SAP ABAP SAP HANA SAP Fiori SAP GRC SAP QM SAP SuccessFactors Salesforce Developer Salesforce Administrator Boomi Dynamics 365 SCM Dynamics 365 Finance Dynamics 365 Customer Service Dynamics 365 Sales Dynamics 365 Customer Voice Dynamics 365 Commerce Dynamics AX Spark Adobe InDesign Oracle Hyperion Planning Customer Support ITIL Blue Prism SAS SCCM SSAS SSIS SSRS Citrix Google AdWords Weblogic Talend UML Human Resource Management Talent Acquisition Power Apps RPA CISCO CISCO DCIM French Apache NiFi Apache Pig TIBCO Spotfire TIBCO Business Studio TIBCO Administration TIBCO ActiveMatrix BPM TIBCO Hawk TIBCO Apache Tomcat Oracle Hyperion Financial Management Oracle Fusion Oracle AIA Oracle APEX Oracle BPM Oracle Apps Oracle Financial Apps Oracle OAF Oracle SOA SAP Hybris SAP BusinessObjects SAP BI SAP PowerDesigner SAP PowerBuilder SAP Leonardo SAP MDM SAP MDG SAP BW SAP SRM SAP UI5 SAP MM SAP HCM SAP BTP (SCP) SAP PI SAP PP SAP Basis SAP SD SAP WM SAP PS SAP BODS SAP DBM SAP Litmos SAP FICO Loadrunner WPF WebFOCUS Ranorex Informatica Data Quality GDPR RabbitMQ Gradle Grunt EJB SnapLogic SharePoint Progress (OpenEdge) Informatica B2B Data Exchange Informatica MDM Joomla Ionic Liferay Sqoop Computer Literacy Communication Skills Technical Support Ecommerce Analytics Software Support Growth Marketing Marketing Analysis Digital Marketing Product Marketing SEO Outreach Market Research Jira German Italian Spanish Grammar & Vocabulary Listening Comprehension Reading Comprehension Sentence Structure
New
Blockchain Drupal Customer Service Project Management Content Strategy Google Analytics Qualitative Analysis Probability Marketing Strategy Email Marketing Dynamics 365 Kubernetes Content Marketing WordPress Sales Informatica Sybase Solidity Administrative Assistance Statistics Google Cloud Platform LLM Content Writing Network Administration Pseudo Code Amazon Redshift SAP B1 Typing
| 🧐 Question | |||||
|---|---|---|---|---|---|
Medium Cookie Security Analysis Web Application Security HTTP Cookies Cross-Domain Communication | Solve | ||||
You are a cybersecurity officer and a new third-party payment gateway is integrated into your company's e-commerce website. The payment gateway API is hosted on a different domain (pay-gateway.com) than your e-commerce site (my-ecommerce.com). You receive some reports that users are unable to complete their transactions intermittently.
You obtain the following set of HTTP cookies from an affected user:
1. user_session=1; Domain=my-ecommerce.com; Path=/; Secure; HttpOnly
2. payment_session=xyz123; Domain=pay-gateway.com; Path=/; Secure; HttpOnly
3. cart_id=abcd1234; Domain=my-ecommerce.com; Path=/; Secure
4. csrf_token=efgh5678; Domain=my-ecommerce.com; Path=/; Secure
5. currency=USD; Domain=my-ecommerce.com; Path=/;
6. same_site_test=1; Domain=my-ecommerce.com; Path=/; Secure; SameSite=None
7. payment_verification=; Domain=my-ecommerce.com; Path=/; Secure; HttpOnly
Which of the following configuration modifications would likely solve the intermittent transaction failure issue?
A: Set SameSite=Strict attribute on all cookies.
B: Set "SameSite=None; Secure" attribute on the payment_session cookie.
C: Change the Domain attribute of payment_session cookie to my-ecommerce.com.
D: Set HttpOnly attribute on cart_id and csrf_token cookies.
E: Remove Secure attribute from user_session cookie.
| |||||
Medium Security Incident Log Analysis | Solve | ||||
You are the security analyst for a company and are currently investigating a security incident. You found the following log entries in your HTTP server logs, which appear to be linked to the incident:
1. 192.0.2.4 - - [24/May/2023:13:15:30 +0000] "GET /wp-login.php HTTP/1.1" 200 167 "-" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
2. 192.0.2.4 - - [24/May/2023:13:15:31 +0000] "POST /wp-login.php HTTP/1.1" 302 152 "http://www.example.com/wp-login.php" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
3. 192.0.2.4 - - [24/May/2023:13:15:32 +0000] "GET /wp-admin/install.php HTTP/1.1" 200 125 "http://www.example.com/wp-admin/" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
Based on this information, which of the following statements are correct?
A: The attacker was unable to compromise the Wordpress login page but was successful in accessing the installation page.
B: The attacker attempted to login to a Wordpress site and, despite the login failing, was able to access the Wordpress installation page.
C: The attacker was attempting a dictionary attack on the Wordpress site and accessed the Wordpress installation page.
D: The logs indicate that the attacker was able to compromise the Wordpress login and directly access the installation page.
E: The attacker attempted to login to a Wordpress site, succeeded, and then tried to access the Wordpress installation page.
| |||||
Medium Network Traffic Anomaly Network Traffic Analysis Network Protocols | Solve | ||||
You are a cybersecurity engineer working on a network traffic analysis case. You have been given the following set of observations from network logs of the past 24 hours:
- Observation 1: 1,000,000 DNS requests were recorded, 50% more than the usual daily traffic.
- Observation 2: 85% of these DNS requests have the same subdomain but different domain names.
- Observation 3: For each of these DNS requests, an HTTP POST request follows immediately.
- Observation 4: No other significant anomalies were detected in the system logs.
Given these observations, what would you suspect is happening?
A: The network is experiencing a DNS amplification attack
B: There is a misconfiguration in the DNS settings
C: The system is the source of a SYN flood attack
D: A fast-flux DNS network is in operation
E: The system is infected with a DNS tunneling based malware
| |||||
Medium SQL Log Analysis SQL Injection Log Analysis | Solve | ||||
You are investigating a possible SQL injection attack on your company's web application. You found the following entries in the HTTP server logs:
Note that each log line contains the following information:
IP Address - Timestamp - Request URI - Request Status - Response Size
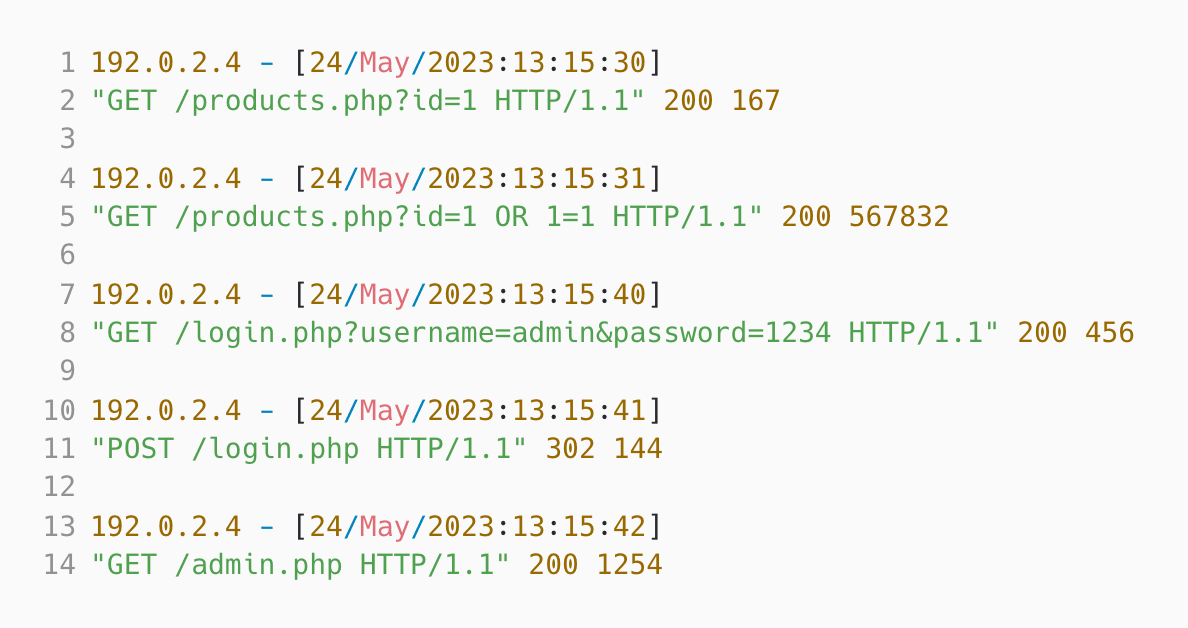 Based on the log entries, which of the following statements are correct? A: The attacker logged in successfully but failed to execute the SQL injection.
B: The attacker failed in the SQL injection attack.
C: The attacker failed to login but successfully accessed the admin page.
D: The attacker performed a successful SQL injection attack that dumped all product information.
E: The attacker was unsuccessful in both the SQL injection attack and the login attempt.
| |||||
Medium Misappropriation Post-Migration DNS Management Infrastructure Migration Subdomain Hijacking | Solve | ||||
A software company decided to move some of their web services from one cloud provider (Vendor A) to another (Vendor B) for better cost optimization. Initially, their main web application "webapp.company.com" was hosted at IP 192.0.2.1 on Vendor A's infrastructure. As part of this transition, it was moved to IP 203.0.113.1 on Vendor B's setup. Subsequently, a secondary web service previously hosted on "serviceA.company.com" at IP 192.0.2.2 (Vendor A), was migrated and re-hosted at "serviceB.company.com" at IP 203.0.113.2 (Vendor B).
A month post-migration, the SEO team reported an unexpected spike in organic traffic to the "company.com" domain. Upon investigating, the IT team noticed unusual activity related to "serviceA.company.com" in the server access logs, including successful HTTP 200 responses from several requests. A suspicious HTTPS GET request, `GET /explicit-content.html HTTP/1.1`, was also recorded.
Running `dig +short serviceA.company.com` returned IP address 198.51.100.1. Cross-checking this information with the company's DNS records revealed:
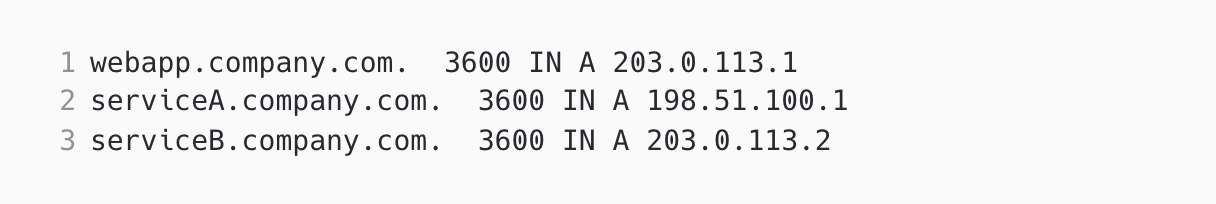 Based on the details provided, identify the probable cause for the unexpected increase in organic traffic: A: The company failed to delete the DNS "A" record for "serviceB.company.com" before migration on vendor A.
B: The company failed to delete the DNS "A" record for "serviceA.company.com" after migration.
C: The company did not configure DNS record for webapp.company.com properly on Vendor B's platform.
D: The DNS configuration for serviceB.company.com is incorrect post migration
| |||||
| 🧐 Question | 🔧 Skill | ||||
|---|---|---|---|---|---|
Medium Cookie Security Analysis Web Application Security HTTP Cookies Cross-Domain Communication | 2 mins Cyber Security | Solve | |||
You are a cybersecurity officer and a new third-party payment gateway is integrated into your company's e-commerce website. The payment gateway API is hosted on a different domain (pay-gateway.com) than your e-commerce site (my-ecommerce.com). You receive some reports that users are unable to complete their transactions intermittently.
You obtain the following set of HTTP cookies from an affected user:
1. user_session=1; Domain=my-ecommerce.com; Path=/; Secure; HttpOnly
2. payment_session=xyz123; Domain=pay-gateway.com; Path=/; Secure; HttpOnly
3. cart_id=abcd1234; Domain=my-ecommerce.com; Path=/; Secure
4. csrf_token=efgh5678; Domain=my-ecommerce.com; Path=/; Secure
5. currency=USD; Domain=my-ecommerce.com; Path=/;
6. same_site_test=1; Domain=my-ecommerce.com; Path=/; Secure; SameSite=None
7. payment_verification=; Domain=my-ecommerce.com; Path=/; Secure; HttpOnly
Which of the following configuration modifications would likely solve the intermittent transaction failure issue?
A: Set SameSite=Strict attribute on all cookies.
B: Set "SameSite=None; Secure" attribute on the payment_session cookie.
C: Change the Domain attribute of payment_session cookie to my-ecommerce.com.
D: Set HttpOnly attribute on cart_id and csrf_token cookies.
E: Remove Secure attribute from user_session cookie.
| |||||
Medium Security Incident Log Analysis | 2 mins Cyber Security | Solve | |||
You are the security analyst for a company and are currently investigating a security incident. You found the following log entries in your HTTP server logs, which appear to be linked to the incident:
1. 192.0.2.4 - - [24/May/2023:13:15:30 +0000] "GET /wp-login.php HTTP/1.1" 200 167 "-" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
2. 192.0.2.4 - - [24/May/2023:13:15:31 +0000] "POST /wp-login.php HTTP/1.1" 302 152 "http://www.example.com/wp-login.php" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
3. 192.0.2.4 - - [24/May/2023:13:15:32 +0000] "GET /wp-admin/install.php HTTP/1.1" 200 125 "http://www.example.com/wp-admin/" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
Based on this information, which of the following statements are correct?
A: The attacker was unable to compromise the Wordpress login page but was successful in accessing the installation page.
B: The attacker attempted to login to a Wordpress site and, despite the login failing, was able to access the Wordpress installation page.
C: The attacker was attempting a dictionary attack on the Wordpress site and accessed the Wordpress installation page.
D: The logs indicate that the attacker was able to compromise the Wordpress login and directly access the installation page.
E: The attacker attempted to login to a Wordpress site, succeeded, and then tried to access the Wordpress installation page.
| |||||
Medium Network Traffic Anomaly Network Traffic Analysis Network Protocols | 2 mins Cyber Security | Solve | |||
You are a cybersecurity engineer working on a network traffic analysis case. You have been given the following set of observations from network logs of the past 24 hours:
- Observation 1: 1,000,000 DNS requests were recorded, 50% more than the usual daily traffic.
- Observation 2: 85% of these DNS requests have the same subdomain but different domain names.
- Observation 3: For each of these DNS requests, an HTTP POST request follows immediately.
- Observation 4: No other significant anomalies were detected in the system logs.
Given these observations, what would you suspect is happening?
A: The network is experiencing a DNS amplification attack
B: There is a misconfiguration in the DNS settings
C: The system is the source of a SYN flood attack
D: A fast-flux DNS network is in operation
E: The system is infected with a DNS tunneling based malware
| |||||
Medium SQL Log Analysis SQL Injection Log Analysis | 2 mins Cyber Security | Solve | |||
You are investigating a possible SQL injection attack on your company's web application. You found the following entries in the HTTP server logs:
Note that each log line contains the following information:
IP Address - Timestamp - Request URI - Request Status - Response Size
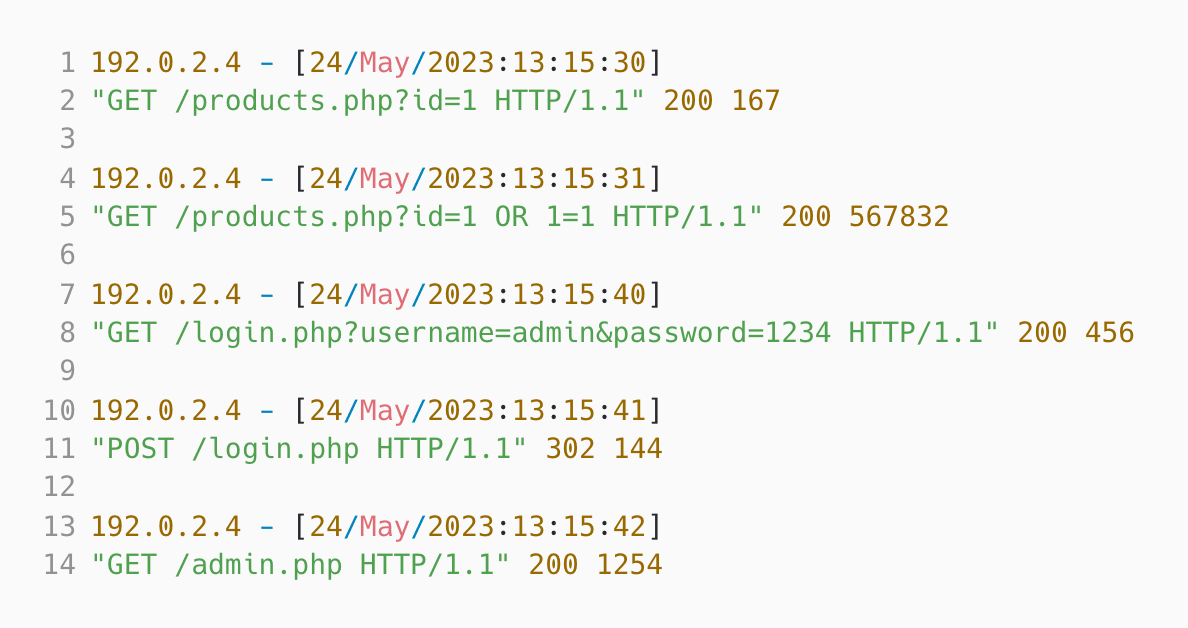 Based on the log entries, which of the following statements are correct? A: The attacker logged in successfully but failed to execute the SQL injection.
B: The attacker failed in the SQL injection attack.
C: The attacker failed to login but successfully accessed the admin page.
D: The attacker performed a successful SQL injection attack that dumped all product information.
E: The attacker was unsuccessful in both the SQL injection attack and the login attempt.
| |||||
Medium Misappropriation Post-Migration DNS Management Infrastructure Migration Subdomain Hijacking | 3 mins Cyber Security | Solve | |||
A software company decided to move some of their web services from one cloud provider (Vendor A) to another (Vendor B) for better cost optimization. Initially, their main web application "webapp.company.com" was hosted at IP 192.0.2.1 on Vendor A's infrastructure. As part of this transition, it was moved to IP 203.0.113.1 on Vendor B's setup. Subsequently, a secondary web service previously hosted on "serviceA.company.com" at IP 192.0.2.2 (Vendor A), was migrated and re-hosted at "serviceB.company.com" at IP 203.0.113.2 (Vendor B).
A month post-migration, the SEO team reported an unexpected spike in organic traffic to the "company.com" domain. Upon investigating, the IT team noticed unusual activity related to "serviceA.company.com" in the server access logs, including successful HTTP 200 responses from several requests. A suspicious HTTPS GET request, `GET /explicit-content.html HTTP/1.1`, was also recorded.
Running `dig +short serviceA.company.com` returned IP address 198.51.100.1. Cross-checking this information with the company's DNS records revealed:
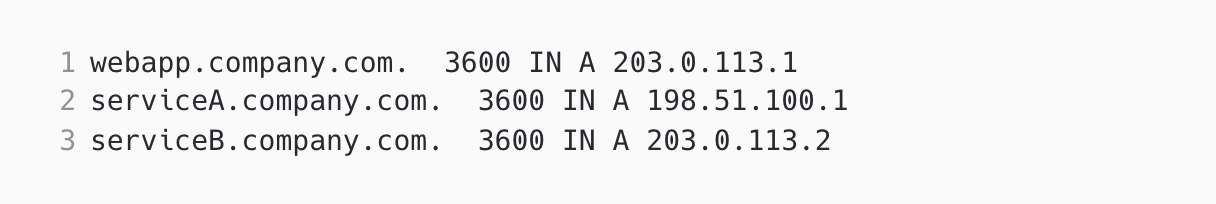 Based on the details provided, identify the probable cause for the unexpected increase in organic traffic: A: The company failed to delete the DNS "A" record for "serviceB.company.com" before migration on vendor A.
B: The company failed to delete the DNS "A" record for "serviceA.company.com" after migration.
C: The company did not configure DNS record for webapp.company.com properly on Vendor B's platform.
D: The DNS configuration for serviceB.company.com is incorrect post migration
| |||||
| 🧐 Question | 🔧 Skill | 💪 Difficulty | ⌛ Time | ||
|---|---|---|---|---|---|
Cookie Security Analysis Web Application Security HTTP Cookies Cross-Domain Communication | Cyber Security | Medium | 2 mins | Solve | |
You are a cybersecurity officer and a new third-party payment gateway is integrated into your company's e-commerce website. The payment gateway API is hosted on a different domain (pay-gateway.com) than your e-commerce site (my-ecommerce.com). You receive some reports that users are unable to complete their transactions intermittently.
You obtain the following set of HTTP cookies from an affected user:
1. user_session=1; Domain=my-ecommerce.com; Path=/; Secure; HttpOnly
2. payment_session=xyz123; Domain=pay-gateway.com; Path=/; Secure; HttpOnly
3. cart_id=abcd1234; Domain=my-ecommerce.com; Path=/; Secure
4. csrf_token=efgh5678; Domain=my-ecommerce.com; Path=/; Secure
5. currency=USD; Domain=my-ecommerce.com; Path=/;
6. same_site_test=1; Domain=my-ecommerce.com; Path=/; Secure; SameSite=None
7. payment_verification=; Domain=my-ecommerce.com; Path=/; Secure; HttpOnly
Which of the following configuration modifications would likely solve the intermittent transaction failure issue?
A: Set SameSite=Strict attribute on all cookies.
B: Set "SameSite=None; Secure" attribute on the payment_session cookie.
C: Change the Domain attribute of payment_session cookie to my-ecommerce.com.
D: Set HttpOnly attribute on cart_id and csrf_token cookies.
E: Remove Secure attribute from user_session cookie.
| |||||
Security Incident Log Analysis | Cyber Security | Medium | 2 mins | Solve | |
You are the security analyst for a company and are currently investigating a security incident. You found the following log entries in your HTTP server logs, which appear to be linked to the incident:
1. 192.0.2.4 - - [24/May/2023:13:15:30 +0000] "GET /wp-login.php HTTP/1.1" 200 167 "-" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
2. 192.0.2.4 - - [24/May/2023:13:15:31 +0000] "POST /wp-login.php HTTP/1.1" 302 152 "http://www.example.com/wp-login.php" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
3. 192.0.2.4 - - [24/May/2023:13:15:32 +0000] "GET /wp-admin/install.php HTTP/1.1" 200 125 "http://www.example.com/wp-admin/" "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0; yie8)"
Based on this information, which of the following statements are correct?
A: The attacker was unable to compromise the Wordpress login page but was successful in accessing the installation page.
B: The attacker attempted to login to a Wordpress site and, despite the login failing, was able to access the Wordpress installation page.
C: The attacker was attempting a dictionary attack on the Wordpress site and accessed the Wordpress installation page.
D: The logs indicate that the attacker was able to compromise the Wordpress login and directly access the installation page.
E: The attacker attempted to login to a Wordpress site, succeeded, and then tried to access the Wordpress installation page.
| |||||
Network Traffic Anomaly Network Traffic Analysis Network Protocols | Cyber Security | Medium | 2 mins | Solve | |
You are a cybersecurity engineer working on a network traffic analysis case. You have been given the following set of observations from network logs of the past 24 hours:
- Observation 1: 1,000,000 DNS requests were recorded, 50% more than the usual daily traffic.
- Observation 2: 85% of these DNS requests have the same subdomain but different domain names.
- Observation 3: For each of these DNS requests, an HTTP POST request follows immediately.
- Observation 4: No other significant anomalies were detected in the system logs.
Given these observations, what would you suspect is happening?
A: The network is experiencing a DNS amplification attack
B: There is a misconfiguration in the DNS settings
C: The system is the source of a SYN flood attack
D: A fast-flux DNS network is in operation
E: The system is infected with a DNS tunneling based malware
| |||||
SQL Log Analysis SQL Injection Log Analysis | Cyber Security | Medium | 2 mins | Solve | |
You are investigating a possible SQL injection attack on your company's web application. You found the following entries in the HTTP server logs:
Note that each log line contains the following information:
IP Address - Timestamp - Request URI - Request Status - Response Size
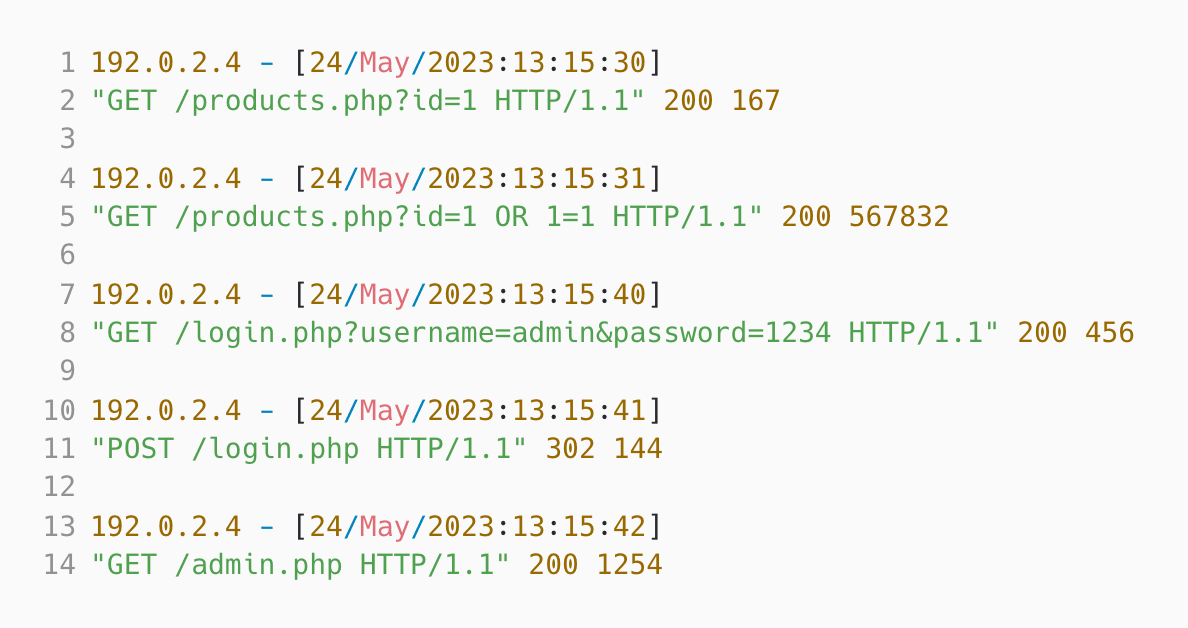 Based on the log entries, which of the following statements are correct? A: The attacker logged in successfully but failed to execute the SQL injection.
B: The attacker failed in the SQL injection attack.
C: The attacker failed to login but successfully accessed the admin page.
D: The attacker performed a successful SQL injection attack that dumped all product information.
E: The attacker was unsuccessful in both the SQL injection attack and the login attempt.
| |||||
Misappropriation Post-Migration DNS Management Infrastructure Migration Subdomain Hijacking | Cyber Security | Medium | 3 mins | Solve | |
A software company decided to move some of their web services from one cloud provider (Vendor A) to another (Vendor B) for better cost optimization. Initially, their main web application "webapp.company.com" was hosted at IP 192.0.2.1 on Vendor A's infrastructure. As part of this transition, it was moved to IP 203.0.113.1 on Vendor B's setup. Subsequently, a secondary web service previously hosted on "serviceA.company.com" at IP 192.0.2.2 (Vendor A), was migrated and re-hosted at "serviceB.company.com" at IP 203.0.113.2 (Vendor B).
A month post-migration, the SEO team reported an unexpected spike in organic traffic to the "company.com" domain. Upon investigating, the IT team noticed unusual activity related to "serviceA.company.com" in the server access logs, including successful HTTP 200 responses from several requests. A suspicious HTTPS GET request, `GET /explicit-content.html HTTP/1.1`, was also recorded.
Running `dig +short serviceA.company.com` returned IP address 198.51.100.1. Cross-checking this information with the company's DNS records revealed:
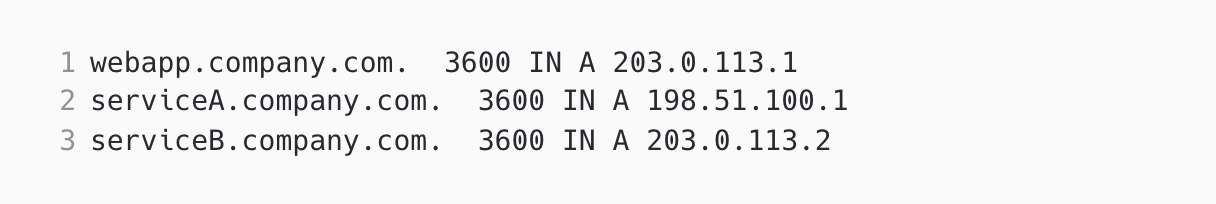 Based on the details provided, identify the probable cause for the unexpected increase in organic traffic: A: The company failed to delete the DNS "A" record for "serviceB.company.com" before migration on vendor A.
B: The company failed to delete the DNS "A" record for "serviceA.company.com" after migration.
C: The company did not configure DNS record for webapp.company.com properly on Vendor B's platform.
D: The DNS configuration for serviceB.company.com is incorrect post migration
| |||||
Trusted by recruitment teams in enterprises globally










We evaluated several of their competitors and found Adaface to be the most compelling. Great library of questions that are designed to test for fit rather than memorization of algorithms.
Swayam Narain, CTO, Affable


Join 1200+ companies in 75+ countries.
Try the most candidate friendly skills assessment tool today.

Ready to streamline your recruitment efforts with Adaface?
Ready to streamline your recruitment efforts with Adaface?
Chat with us
Product
Usecases
© 2023 Adaface Pte. Ltd.
🌎 Pick your language